A brand new report from cloud safety firm Zscaler sheds mild on the rising cell threats on Android working programs, in addition to IoT and OT units threats. The findings come as greater than 60% of the worldwide Web site visitors is now generated by cell units and financially-oriented cell threats have grown by 111% during the last 12 months.
An inventory of cell malware threats
Zscaler’s ThreatLabz witnessed a 29% rise in banking cell malware over the earlier 12 months, with banking malware representing 20% of the whole Android menace panorama.
Most energetic banking malware households so far embody:
Vultur, which is primarily distributed via the Google Play Retailer.
Hydra, distributed by way of phishing messages, web sites, and malicious Google Play Retailer purposes.
Ermac, designed to steal monetary knowledge from banking and pockets apps.
Anatsa, also referred to as TeaBot
Coper, also referred to as Octo
Nexus, primarily targets cryptocurrency accounts
Most of those banking malware file keystrokes, hijack credentials, and intercept SMS messages so as to bypass Multi-Issue Authentication.
SEE: Tips on how to Create an Efficient Cybersecurity Consciousness Program (TechRepublic Premium)
Adware threats soar by greater than 100%
Along with banking malware, adware threats have additionally grown, with researchers indicating that blocked transactions elevated by 100% over the earlier 12 months.
Probably the most prevalent adware reported are SpyLoan, SpinOk, and SpyNote.
SpyLoan has the power to steal private knowledge from units, resembling accounts, system info, name logs, put in apps, calendar occasions, metadata, and extra.
SpinOk adware collects delicate knowledge and recordsdata from numerous places on the contaminated system and exfiltrates the information to an attacker-controlled server.
SpyNote, also referred to as CypherRat, supplies further distant entry capabilities in order that the attacker can management execution of software program on the cell system.
In keeping with Zscaler, most cell malware focused India (28%), the U.S. (27%), and Canada (15%), adopted by South Africa (6%), The Netherlands (5%), Mexico (4%), Nigeria (3%), Brazil (3%), Singapore (3%) and the Philippines (2%).
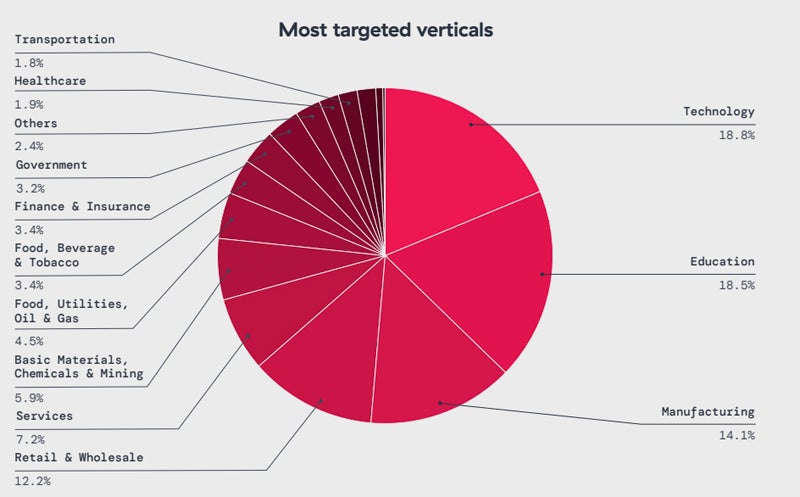
Impacted sectors embody know-how (18%), training (18%), manufacturing (14%), retail and wholesale (12%), and providers (7%).
Cellular malware are distributed by way of numerous strategies. One technique consists of utilizing social engineering methods. For instance, Zscaler studies that attackers deployed the Copybara cell malware by utilizing voice phishing (vishing) assaults, the place the sufferer acquired voice directions to put in the malware on their Android telephones.
QR code rip-off can also be widespread, the place victims are tricked into scanning malicious QR codes resulting in malware infections or, in some instances, to phishing pages.
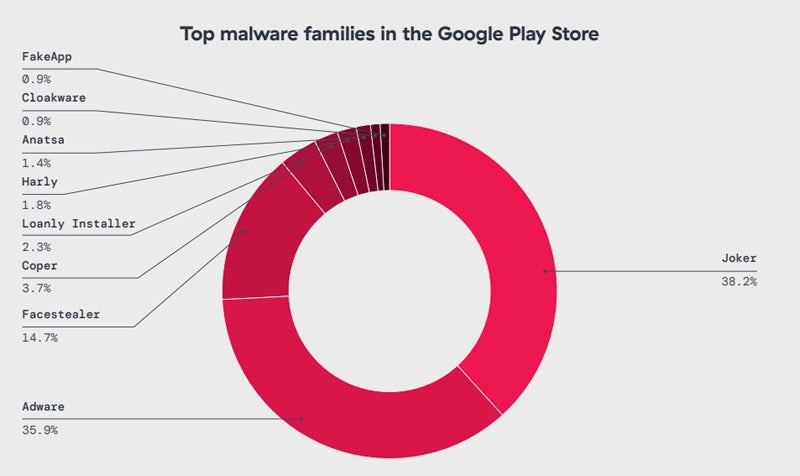
Some malware can also be obtainable on the Google Play Retailer. This consists of Joker — which silently subscribes customers to premium providers with out their consent to generate prices — adopted by adware malware sort and facestealer, a Fb account stealer.
General, regardless of an general lower in Android assaults, financially-oriented cell threats have grown by 111% during the last 12 months.
Should-read safety protection
IoT and OT threats
Web of Issues and Operational Expertise environments maintain increasing and are more and more focused by attackers, in keeping with the report. The researchers point out that the variety of IoT units interacting with them has grown by 37% year-over-year.
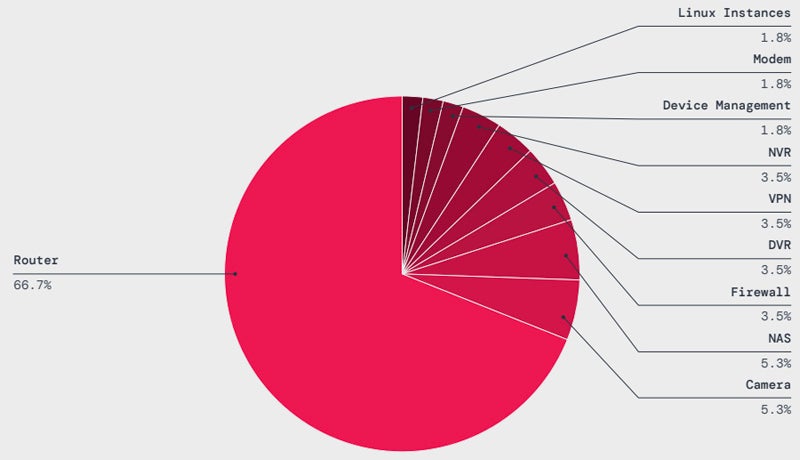
IoT malware assaults have grown by 45% over the previous 12 months, with routers being essentially the most focused sort of system, with greater than 66% of assaults geared toward these units. The main malware households hitting IoT units are Mirai (36.3%) and Gafgyt (21.2%). Botnets constructed with these malware on IoT units can be utilized to launch giant Distributed Denial of Service assaults.
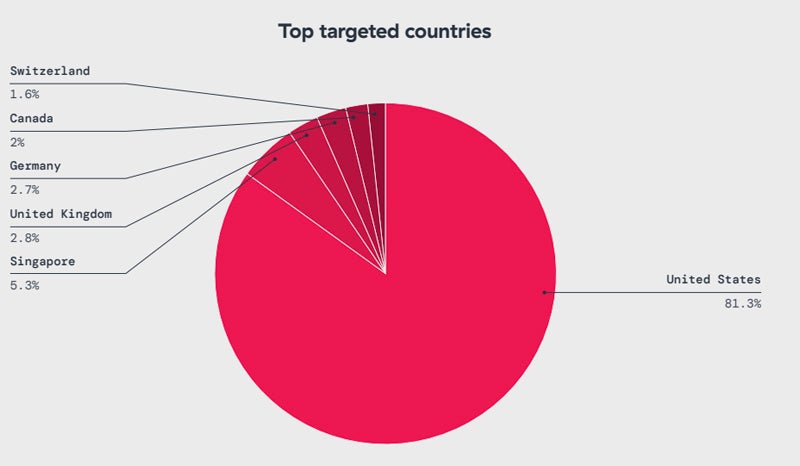
Relating to the geographical distribution, greater than 81% of IoT malware assaults are aimed on the U.S., adopted by Singapore (5.3%), the UK (2.8%), Germany (2.7%), Canada (2%), and Switzerland (1.6%).
High sectors impacted by IoT malware assaults are manufacturing (36.9%), transportation (14.2%), meals, beverage, and tobacco (11.1%).
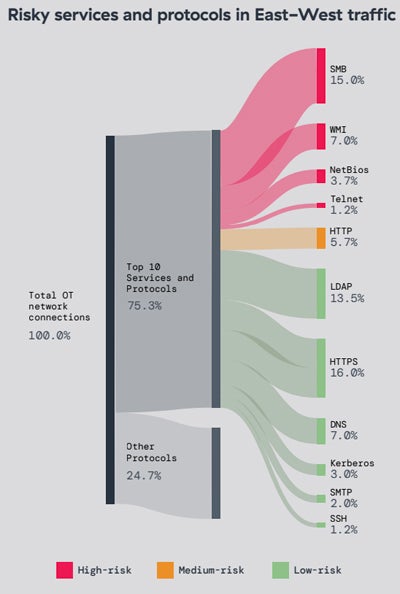
On the OT aspect, 50% of the units in lots of deployments use legacy, end-of-life working programs. Protocols susceptible to totally different vulnerabilities are additionally typically uncovered in OT environments, resembling SMB or WMI.
For instance, ThreatLabz analyzed the OT content material of a large-scale manufacturing group, comprising greater than 17,000 linked OT units throughout greater than 40 totally different places. Every website contained greater than 500 OT units with end-of-life Microsoft Home windows working programs, lots of which had recognized vulnerabilities.
67% of the worldwide site visitors to the OT units was unauthorized or blocked.
What is going to the long run seem like?
In keeping with Zscaler, IoT and OT units will stay main menace vectors, whereas the manufacturing sector will stay a prime goal for IoT assaults, together with ransomware.
Zscaler additionally suspects synthetic intelligence will probably be more and more used to ship high-quality phishing campaigns focusing on cell customers. Nevertheless, AI can even assist defenders automate crucial capabilities and higher prioritize their efforts.
Tips on how to defend IoT and OT units from cyber assaults
To guard from threats on IoT and OT units, it’s essential to:
Achieve visibility on IoT and OT units is a precedence. Organizations want to find, classify, and preserve lists of all IoT and OT units used of their full atmosphere.
Maintain all programs and software program updated and patched to stop being compromised by widespread vulnerabilities.
Community logs have to be collected and analyzed. Suspicious person account entry and system occasions have to be notably monitored.
Multi-factor authentication have to be deployed when doable, and default passwords and accounts have to be modified or disabled.
Zero-Belief system segmentation needs to be enforced for IoT and OT property to reduce knowledge publicity.
Tips on how to defend cell units from cyber assaults
To guard from threats on cell units, you will need to:
Set up safety purposes on the units, to guard them from malware and doable phishing makes an attempt.
Any hyperlink arriving on the cell phone, irrespective of the applying, needs to be cautiously examined. In case of suspicious hyperlink, it should not be clicked and reported to IT safety employees.
Unknown purposes have to be prevented. Additionally, purposes ought to by no means be downloaded from third events or untrusted sources.
Corporations must also be cautious of purposes requesting updates instantly after set up. An software downloaded from the Play Retailer needs to be the newest model. If an app requests permission to replace instantly after set up, it needs to be handled as suspicious and will point out malware trying to obtain further malicious elements.
Disclosure: I work for Pattern Micro, however the views expressed on this article are mine.


_SunFlowerStudio_Alamy.jpg?disable=upscale&width=1200&height=630&fit=crop)