Introduction
Linux servers are identified for his or her reliability and safety, which has made them in style in each enterprise and particular person deployments. Nonetheless, no system is impervious to assaults. With cyber threats evolving continually, server directors should undertake proactive measures to safe their methods towards vulnerabilities and assaults. This information dives into a spread of hardening strategies and greatest practices to create a fortified Linux setting that’s resilient towards numerous threats.
Understanding the Risk Panorama
Earlier than diving into particular measures, it’s important to know the forms of threats Linux servers could encounter. These embrace:
Brute-Pressure Assaults: Makes an attempt to achieve unauthorized entry by systematically making an attempt all doable combos of passwords.
Rootkits and Malware: Malicious software program that may acquire unauthorized entry to server assets.
Denial of Service (DoS) Assaults: Overloading server assets, rendering companies unavailable.
Zero-Day Vulnerabilities: Exploits concentrating on unknown or unpatched vulnerabilities within the system.
Understanding these potential threats is step one to constructing an efficient safety technique.
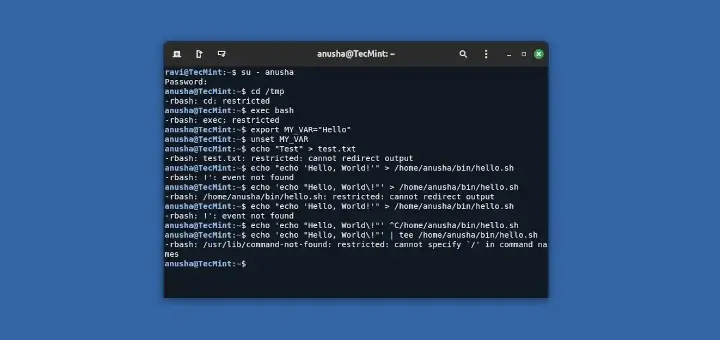
Consumer and Entry Management
Probably the most important facets of server safety is managing person entry successfully. Limiting who can entry your server and the way they’ll achieve this is important in decreasing danger.
Consumer Administration and Privilege Separation
Keep away from Direct Root Entry: Utilizing root instantly could make the server extra weak. As an alternative, create a brand new person with sudo privileges for administrative duties.
Implement Precept of Least Privilege: Assign solely the mandatory permissions required to finish particular duties, stopping customers from accessing delicate areas they don’t want.
Repeatedly Evaluation Consumer Accounts: Take away previous or inactive accounts to keep away from potential entry factors for attackers.
SSH Hardening
Disable Root Login Over SSH: Modify the /and many others/ssh/sshd_config file to disallow root login by setting PermitRootLogin no.
Allow Key-Primarily based Authentication: Keep away from utilizing password-based authentication for SSH by organising public-private key pairs. This reduces the chance of brute-force assaults.
Limit SSH Entry by IP: Configure firewall guidelines or use TCP wrappers to restrict SSH entry to particular IP addresses.
Multi-Issue Authentication (MFA)
Set Up MFA for SSH: Use instruments like Google Authenticator or Duo Safety to allow MFA, including an additional layer of safety to the authentication course of.
Configuration: Set up an MFA app in your cellphone, then configure it on the server, and arrange the /and many others/pam.d/sshd file to implement MFA for SSH.
Safe System Configuration
System Updates and Patch Administration
Allow Automated Updates: Configure your package deal supervisor to put in safety patches mechanically. This may be finished with instruments like unattended-upgrades on Debian-based methods or yum-cron on CentOS/RHEL.
Repeatedly Verify for Vulnerabilities: Use vulnerability scanners like Lynis or OpenVAS to determine any weaknesses in your present configuration.
Kernel Safety Settings
Sysctl Hardening: Modify kernel parameters with sysctl to boost safety. For instance:
Disable IP forwarding: internet.ipv4.ip_forward = 0
Forestall ICMP (ping) requests: internet.ipv4.icmp_echo_ignore_all = 1
Use Safety Modules: Linux helps extra modules like grsecurity (for hardened kernels) or SELinux, which offer superior entry management to delicate areas.
Community Configuration
Disable Unused Ports and Companies: Shut all pointless ports and disable companies not required to your server’s operation. Use netstat or ss to examine for open ports.
Firewall Configuration: Arrange iptables or firewalld to outline strict guidelines for incoming and outgoing visitors. Solely enable important companies and block every part else by default.
Superior Authentication and Authorization Mechanisms
Position-Primarily based Entry Management (RBAC)
Utilizing RBAC: RBAC lets you outline roles with particular privileges and assign customers to those roles, minimizing extreme permissions.
Implementing RBAC with Sudo and Consumer Teams: Use the sudo command to manage which instructions particular customers can run. Moreover, group customers with related roles to centralize permission administration.
Utilizing SELinux and AppArmor
SELinux: Enforces safety insurance policies that restrict how purposes can work together with the system. Configure SELinux insurance policies to dam unauthorized entry or limit applications to their needed features.
AppArmor: Much like SELinux, AppArmor confines purposes to a specified set of assets, blocking any try and entry assets exterior the outlined coverage.
Utility and Database Safety
Securing Internet Purposes
Configuring Apache/Nginx: Set restrictive permissions for delicate directories and allow HTTPS by default. Repeatedly replace the server software program to stop vulnerabilities.
Internet Utility Firewall (WAF): Use a WAF like ModSecurity to filter and monitor HTTP requests, including a layer of safety to your net purposes.
Database Hardening
Limit Database Entry: Restrict the IP addresses that may entry your database to trusted hosts solely. That is particularly important in case your database is accessible from the web.
Encrypt Delicate Information: Use database-level encryption and think about full-disk encryption to guard information at relaxation.
SQL Injection Safety: Validate all inputs and use ready statements to stop SQL injection assaults.
Auditing, Monitoring, and Logging
Setting Up Logging with Syslog and JournalD
Log Configuration: Allow logging for key companies and purposes. Use Syslog or JournalD to centralize and monitor logs.
Log Rotation: Configure logrotate to handle and archive logs to stop disk area from being exhausted.
Utilizing Actual-Time Monitoring Instruments
Fail2ban: Screens logs and bans IPs after a particular variety of failed login makes an attempt, serving to stop brute-force assaults.
Intrusion Detection Instruments: Instruments like Tripwire and OSSEC can detect unauthorized adjustments in recordsdata or uncommon exercise.
Auditing with Auditd
Setting Up Audit Guidelines: Configure Auditd to watch entry to delicate recordsdata and directories. Audit guidelines can monitor login makes an attempt, file modifications, and different important occasions.
Common Audits: Schedule periodic audits to overview logs and analyze any suspicious patterns or anomalies.
Information Safety and Encryption
Encrypting Information at Relaxation and In-Transit
Disk Encryption with LUKS: For delicate information, think about full-disk encryption utilizing LUKS. This prevents information from being accessed if the storage gadget is eliminated or stolen.
TLS for In-Transit Information: Implement HTTPS on all net servers to encrypt information throughout transmission. Moreover, use TLS for any database connections to guard information in transit.
File Integrity Monitoring
AIDE for Integrity Checks: Superior Intrusion Detection Surroundings (AIDE) is a device that detects file modifications, deletions, or additions. Configure AIDE to carry out every day scans and ship alerts on detecting unauthorized adjustments.
Incident Response and Backup Technique
Planning for Incident Response
Develop an Incident Response Plan: Define steps for detecting, containing, and recovering from safety incidents. Embrace roles, duties, and communication protocols.
Safety Data and Occasion Administration (SIEM): Think about implementing SIEM instruments for real-time occasion correlation, which helps in speedy detection and response.
Automated Backups and Restoration
Backup Frequency: Configure common automated backups utilizing instruments like rsync and cron. Retailer backups in a number of places, together with offsite or cloud storage.
Testing Restoration Procedures: Repeatedly take a look at backup restoration processes to make sure information recoverability in case of a breach or information loss.
Conclusion
Securing a Linux server requires a multi-layered strategy that features person administration, system configuration, software hardening, and a stable incident response technique. By implementing the practices mentioned on this information, you’ll have a fortified Linux server that’s well-prepared to face at the moment’s subtle risk panorama. Keep in mind, sustaining safety is an ongoing course of that requires vigilance, common updates, and proactive monitoring.
George Whittaker is the editor of Linux Journal, and likewise a daily contributor. George has been writing about expertise for twenty years, and has been a Linux person for over 15 years. In his free time he enjoys programming, studying, and gaming.





![Best AI Audio Enhancer: Top 10 Solutions [Free & Paid] Best AI Audio Enhancer: Top 10 Solutions [Free & Paid]](https://mspoweruser.com/wp-content/uploads/2024/10/best-ai-audio-enhancer.jpg)


/cdn.vox-cdn.com/uploads/chorus_asset/file/24402139/STK071_apple_K_Radtke_03.jpg)















