The sufferer shaming web site operated by the Snatch ransomware group is leaking information about its true on-line location and inside operations, in addition to the Web addresses of its guests, KrebsOnSecurity has discovered. The leaked information recommend that Snatch is considered one of a number of ransomware teams utilizing paid advertisements on Google.com to trick folks into putting in malware disguised as fashionable free software program, equivalent to Microsoft Groups, Adobe Reader, Mozilla Thunderbird, and Discord.
First noticed in 2018, the Snatch ransomware group has revealed information stolen from a whole lot of organizations that refused to pay a ransom demand. Snatch publishes its stolen information at an internet site on the open Web, and that content material is mirrored on the Snatch crew’s darknet web site, which is barely reachable utilizing the worldwide anonymity community Tor.
The sufferer shaming web site for the Snatch ransomware gang.
KrebsOnSecurity has realized that Snatch’s darknet web site exposes its “server standing” web page, which incorporates details about the true Web addresses of customers accessing the web site.
Refreshing this web page each few seconds reveals that the Snatch darknet web site generates a good quantity of site visitors, usually attracting hundreds of tourists every day. However by far probably the most frequent repeat guests are coming from Web addresses in Russia that both at the moment host Snatch’s clear net domains or lately did.
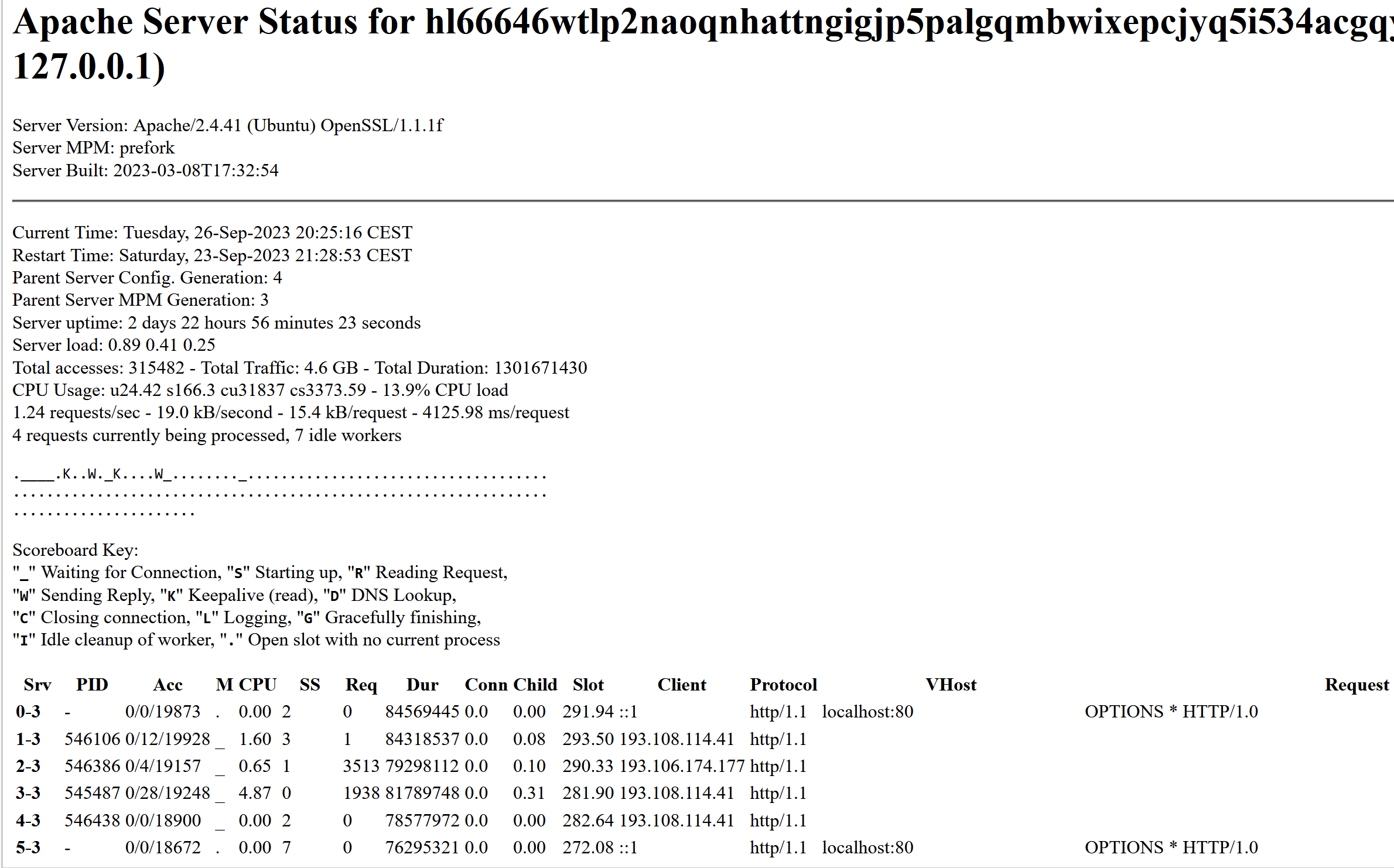
The Snatch ransomware gang’s sufferer shaming web site on the darknet is leaking information about its guests. This “server standing” web page says that Snatch’s web site is on Central European Summer time Time (CEST) and is powered by OpenSSL/1.1.1f, which is not supported by safety updates.
In all probability probably the most energetic Web deal with accessing Snatch’s darknet web site is 193.108.114[.]41, which is a server in Yekaterinburg, Russia that hosts a number of Snatch domains, together with snatchteam[.]high, sntech2ch[.]high, dwhyj2[.]high and sn76930193ch[.]high. It might nicely be that this Web deal with is exhibiting up incessantly as a result of Snatch’s clear-web web site incorporates a toggle button on the high that lets guests swap over to accessing the location through Tor.
One other Web deal with that confirmed up incessantly within the Snatch server standing web page was 194.168.175[.]226, at the moment assigned to Matrix Telekom in Russia. Based on DomainTools.com, this deal with additionally hosts or else lately hosted the same old coterie of Snatch domains, in addition to fairly a number of domains phishing identified manufacturers equivalent to Amazon and Cashapp.
The Moscow Web deal with 80.66.64[.]15 accessed the Snatch darknet web site all day lengthy, and that deal with additionally housed the suitable Snatch clear-web domains. Extra apparently, that deal with is residence to a number of latest domains that seem confusingly much like identified software program firms, together with libreoff1ce[.]com and www-discord[.]com.
That is attention-grabbing as a result of the phishing domains related to the Snatch ransomware gang had been all registered to the identical Russian identify — Mihail Kolesnikov, a reputation that’s considerably synonymous with latest phishing domains tied to malicious Google advertisements.
Kolesnikov may very well be a nod to a Russian common made well-known throughout Boris Yeltsin’s reign. Both means, it’s clearly a pseudonym, however there are another commonalities amongst these domains which will present perception into how Snatch and different ransomware teams are sourcing their victims.
DomainTools says there are greater than 1,300 present and former domains registered to Mihail Kolesnikov between 2013 and July 2023. About half of the domains look like older web sites promoting feminine escort providers in main cities round the USA (e.g. the now-defunct pittsburghcitygirls[.]com).
The opposite half of the Kolesnikov web sites are far newer phishing domains largely ending in “.high” and “.app” that seem designed to imitate the domains of main software program firms, together with www-citrix[.]high, www-microsofteams[.]high, www-fortinet[.]high, ibreoffice[.]high, www-docker[.]high, www-basecamp[.]high, ccleaner-cdn[.]high, adobeusa[.]high, and www.real-vnc[.]high.
In August 2023, researchers with Trustwave Spiderlabs stated they encountered domains registered to Mihail Kolesnikov getting used to disseminate the Rilide info stealer trojan.
However it seems a number of crime teams could also be utilizing these domains to phish folks and disseminate all types of information-stealing malware. In February 2023, Spamhaus warned of an enormous surge in malicious advertisements that had been hijacking search ends in Google.com, and getting used to distribute at the very least 5 completely different households of data stealing trojans, together with AuroraStealer, IcedID/Bokbot, Meta Stealer, RedLine Stealer and Vidar.
For instance, Spamhaus stated victims of those malicious advertisements would seek for Microsoft Groups in Google.com, and the search engine would usually return a paid advert spoofing Microsoft or Microsoft Groups as the primary outcome — above all different outcomes. The malicious advert would come with a emblem for Microsoft and at first look look like a secure and trusted place to obtain the Microsoft Groups consumer.
Nevertheless, anybody who clicked on the outcome was whisked away as a substitute to mlcrosofteams-us[.]high — one more malicious area registered to Mr. Kolesnikov. And whereas guests to this web site could consider they’re solely downloading the Microsoft Groups consumer, the installer file features a copy of the IcedID malware, which is actually good at stealing passwords and authentication tokens from the sufferer’s net browser.
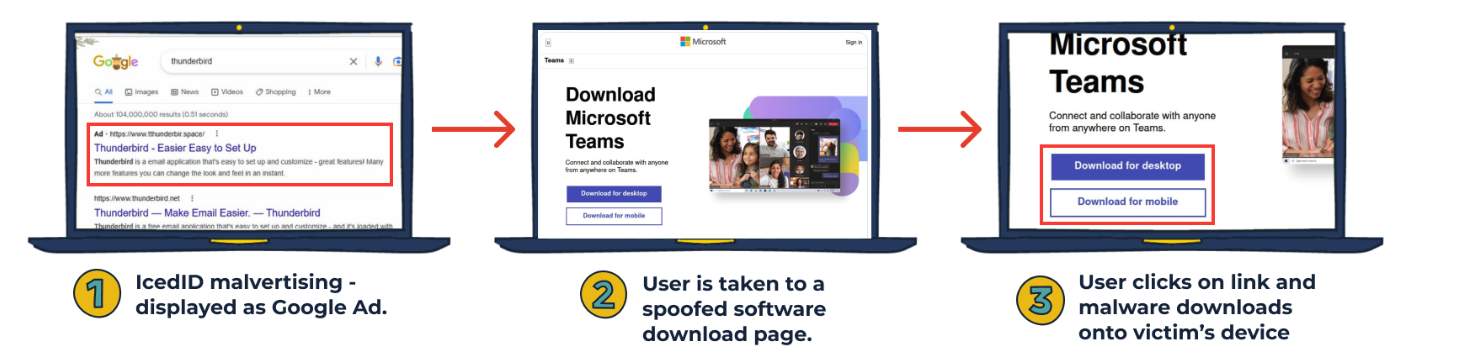
Picture: Spamhaus
The founding father of the Swiss anti-abuse web site abuse.ch instructed Spamhaus it’s doubtless that some cybercriminals have began to promote “malvertising as a service” on the darkish net, and that there’s a substantial amount of demand for this service.
In different phrases, somebody seems to have constructed a really worthwhile enterprise churning out and selling new software-themed phishing domains and promoting that as a service to different cybercriminals. Or maybe they’re merely promoting any stolen information (and any company entry) to energetic and hungry ransomware group associates.
The tip concerning the uncovered “server standing” web page on the Snatch darkweb web site got here from @htmalgae, the identical safety researcher who alerted KrebsOnSecurity earlier this month that the darknet sufferer shaming web site run by the 8Base ransomware gang was inadvertently left in growth mode.
That oversight revealed not solely the true Web deal with of the hidden 8Base web site (in Russia, naturally), but additionally the id of a programmer in Moldova who apparently helped to develop the 8Base code.
@htmalgae stated the concept of a ransomware group’s sufferer shaming web site leaking information that they didn’t intend to reveal is deliciously ironic.
“This can be a prison group that shames others for not defending person information,” @htmalgae stated. “And right here they’re leaking their person information.”
All the malware talked about on this story is designed to run on Microsoft Home windows gadgets. However Malwarebytes lately coated the emergence of a Mac-based info stealer trojan known as AtomicStealer that was being marketed via malicious Google advertisements and domains that had been confusingly much like software program manufacturers.
Please be additional cautious if you end up looking on-line for fashionable software program titles. Cracked, pirated copies of main software program titles are a frequent supply of infostealer infections, as are these rogue advertisements masquerading as search outcomes. Make sure that to double-check you might be really on the area you consider you’re visiting *earlier than* you obtain and set up something.
Keep tuned for Half II of this put up, which features a nearer take a look at the Snatch ransomware group and their founder.
Additional studying:
@HTMalgae’s record of the highest Web addresses seen accessing Snatch’s darknet web site
Ars Technica: Till Additional Discover Suppose Twice Earlier than Utilizing Google to Obtain Software program
Bleeping Pc: Hackers Abuse Google Adverts to Unfold Malware in Legit Software program


























