The pretend USPS phishing web page.
Latest weeks have seen a large uptick within the variety of phishing scams concentrating on U.S. Postal Service (USPS) clients. Right here’s a take a look at an in depth SMS phishing operation that tries to steal private and monetary information by spoofing the USPS, in addition to postal providers in at the least a dozen different international locations.
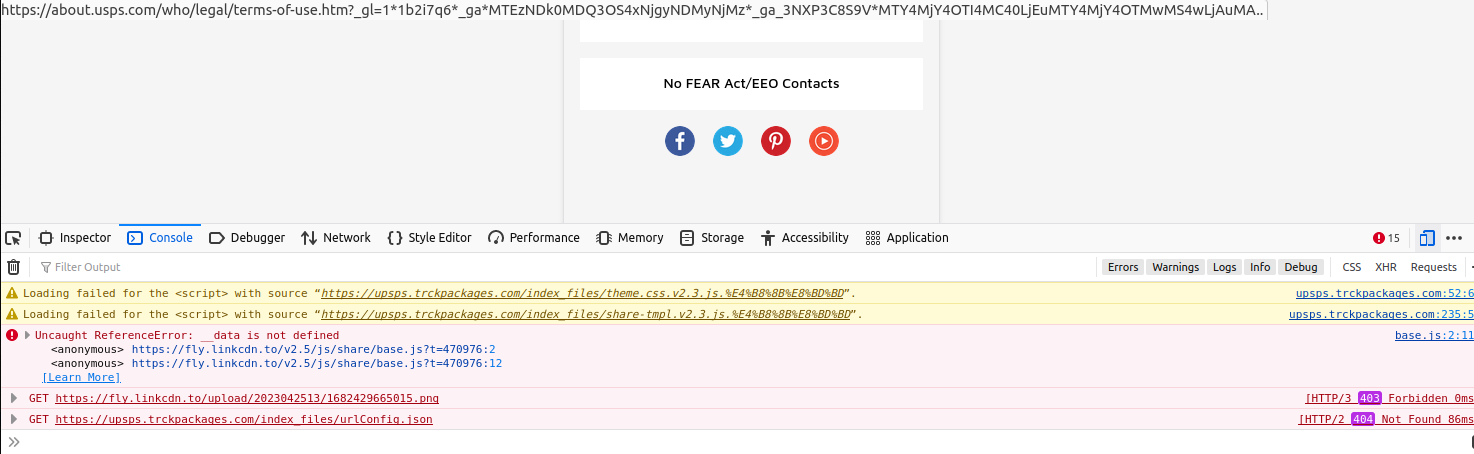
KrebsOnSecurity just lately heard from a reader who acquired an SMS purporting to have been despatched by the USPS, saying there was an issue with a bundle destined for the reader’s deal with. Clicking the hyperlink within the textual content message brings one to the area usps.informedtrck[.]com.
The touchdown web page generated by the phishing hyperlink consists of the USPS brand, and says “Your bundle is on maintain for an invalid recipient deal with. Fill within the right deal with information by the hyperlink.” Beneath that message is a “Click on replace” button that takes the customer to a web page that asks for extra data.
The remaining buttons on the phishing web page all hyperlink to the actual USPS.com web site. After accumulating your deal with data, the pretend USPS website goes on to request extra private and monetary information.
This phishing area was just lately registered and its WHOIS possession information are mainly nonexistent. Nonetheless, we will discover some compelling clues in regards to the extent of this operation by loading the phishing web page in Developer Instruments, a set of debugging options constructed into Firefox, Chrome and Safari that permit one to intently examine a webpage’s code and operations.
Try the underside portion of the screenshot beneath, and also you’ll discover that this phishing website fails to load some exterior assets, together with a picture from a hyperlink referred to as fly.linkcdn[.]to.
Click on the picture to enlarge.
A search on this area on the always-useful URLscan.io reveals that fly.linkcdn[.]to is tied to a slew of USPS-themed phishing domains. Listed here are just some of these domains (hyperlinks defanged to stop unintentional clicking):
usps.receivepost[.]comusps.informedtrck[.]comusps.trckspost[.]compostreceive[.]comusps.trckpackages[.]comusps.infortrck[.]comusps.quicktpos[.]comusps.postreceive].]comusps.revepost[.]comtrackingusps.infortrck[.]comusps.receivepost[.]comusps.trckmybusi[.]compostreceive[.]comtackingpos[.]comusps.trckstamp[.]comusa-usps[.]shopusps.infortrck[.]comunlistedstampreceive[.]comusps.stampreceive[.]comusps.stamppos[.]comusps.stampspos[.]comusps.trckmypost[.]comusps.trckintern[.]comusps.tackingpos[.]comusps.posinformed[.]com
As we will see within the screenshot beneath, the developer instruments console for informedtrck[.]com complains that the location is unable to load a Google Analytics code — UA-80133954-3 — which apparently was rejected for pointing to an invalid area.
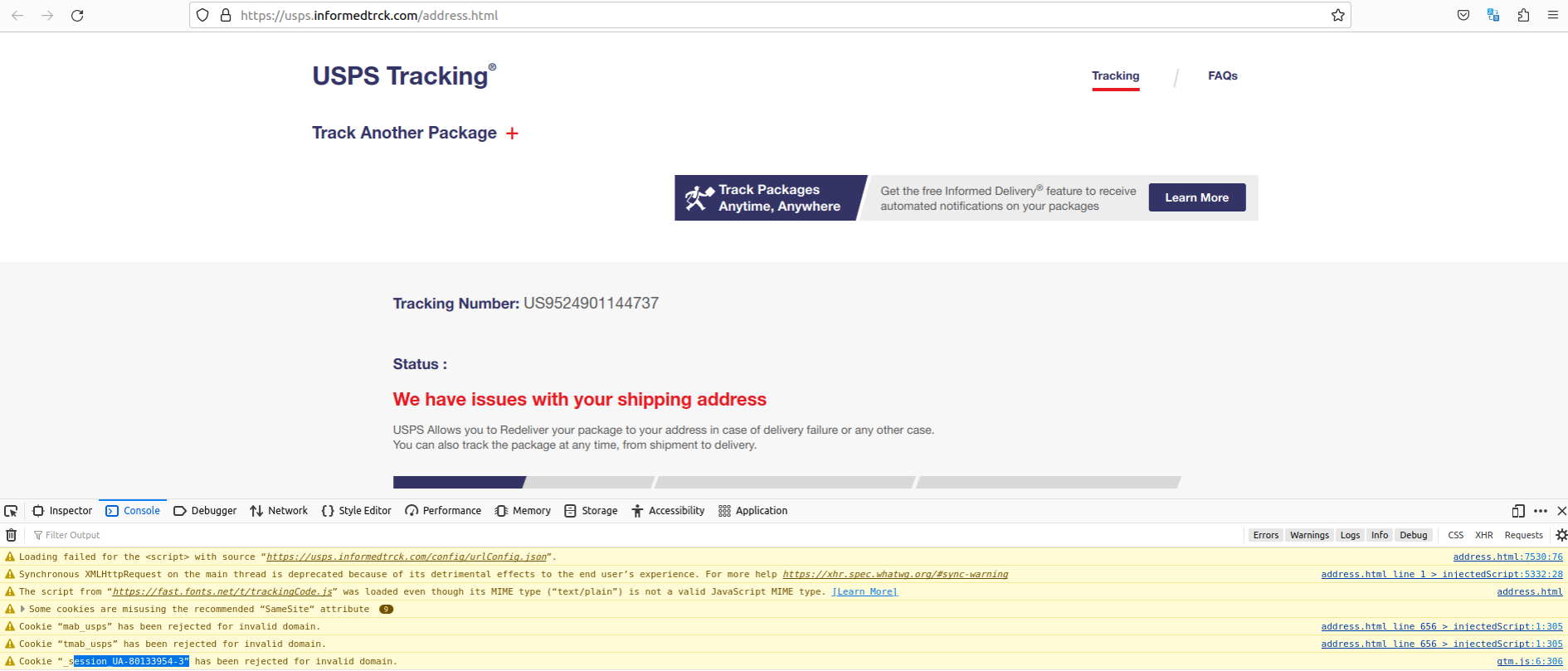
Discover the highlighted Google Analytics code uncovered by a defective Javascript component on the phishing web site. Click on to enlarge. That code truly belongs to the USPS.
The legitimate area for that Google Analytics code is the official usps.com web site. In line with dnslytics.com, that very same analytics code has proven up on at the least six different practically equivalent USPS phishing pages relationship again practically as a few years, together with onlineuspsexpress[.]com, which DomainTools.com says was registered manner again in September 2018 to a person in Nigeria.
A unique area with that very same Google Analytics code that was registered in 2021 is peraltansepeda[.]com, which archive.org reveals was operating the same set of phishing pages concentrating on USPS customers. DomainTools.com signifies this web site identify was registered by phishers primarily based in Indonesia.
DomainTools says the above-mentioned USPS phishing area stamppos[.]com was registered in 2022 by way of Singapore-based Alibaba.com, however the registrant metropolis and state listed for that area says “Georgia, AL,” which isn’t an actual location.
Alas, operating a seek for domains registered by means of Alibaba to anybody claiming to reside in Georgia, AL reveals practically 300 latest postal phishing domains ending in “.high.” These domains are both administrative domains obscured by a password-protected login web page, or are .high domains phishing clients of the USPS in addition to postal providers serving different international locations.
These different nations embrace the Australia Submit, An Submit (Eire), Correos.es (Spain), the Costa Rican submit, the Chilean Submit, the Mexican Postal Service, Poste Italiane (Italy), PostNL (Netherlands), PostNord (Denmark, Norway and Sweden), and Posti (Finland). An entire listing of those domains is accessible right here (PDF).
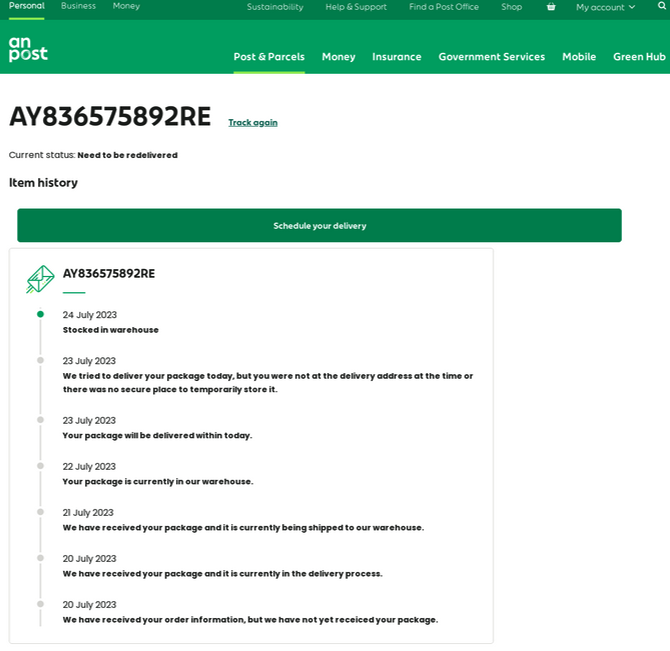
A phishing web page concentrating on An Submit, the state-owned supplier of postal providers in Eire.
The Georgia, AL domains at Alibaba additionally embody a number of that spoof websites claiming to gather excellent street toll charges and fines on behalf of the governments of Australia, New Zealand and Singapore.
An nameless reader wrote in to say they submitted pretend data to the above-mentioned phishing website usps.receivepost[.]com by way of the malware sandbox any.run. A video recording of that evaluation reveals that the location sends any submitted information by way of an automatic bot on the Telegram immediate messaging service.
The visitors evaluation slightly below the any.run video reveals that any information collected by the phishing website is being despatched to the Telegram consumer @chenlun, who affords to promote custom-made supply code for phishing pages. From a overview of @chenlun’s different Telegram channels, it seems this account is being massively spammed for the time being — probably due to public consideration introduced by this story.

In the meantime, researchers at DomainTools just lately revealed a report on an apparently unrelated however equally sprawling SMS-based phishing marketing campaign concentrating on USPS clients that seems to be the work of cybercriminals primarily based in Iran.
Phishers are inclined to solid a large internet and sometimes spoof entities which might be broadly utilized by the native inhabitants, and few manufacturers are going to have extra family attain than home mail providers. In June, the United Parcel Service (UPS) disclosed that fraudsters had been abusing an internet cargo monitoring software in Canada to ship extremely focused SMS phishing messages that spoofed the UPS and different manufacturers.
With the vacation procuring season practically upon us, now is a superb time to remind household and mates about the most effective recommendation to sidestep phishing scams: Keep away from clicking on hyperlinks or attachments that arrive unbidden in emails, textual content messages and different mediums. Most phishing scams invoke a temporal component that warns of damaging penalties must you fail to reply or act shortly.
In the event you’re not sure whether or not the message is official, take a deep breath and go to the location or service in query manually — ideally, utilizing a browser bookmark in order to keep away from potential typosquatting websites.
Replace: Added details about the Telegram bot and any.run evaluation.






















/cdn.vox-cdn.com/uploads/chorus_asset/file/25661290/Screenshot_2024_10_06_at_10.48.36_AM.png)



