This Safari vulnerability has not been exploited within the wild. Apple presents a mitigation, however the repair must be enabled manually.
Safety researchers from three universities have found a serious vulnerability in Apple’s iOS and macOS, together with the Safari browser. The vulnerability, which the researchers named iLeakage, allows risk actors to learn Gmail messages, reveal passwords and uncover different private info.
The vulnerability impacts macOS or iOS units working on Apple’s A-series or M-series CPUs, which embrace all trendy iPhones and iPads, and laptops or desktops launched since 2020. Macs can solely be attacked when utilizing Safari, however cellular units are susceptible when utilizing any browser.
The researchers disclosed their findings to Apple on Sept. 12, 2022, and made the findings, in addition to a analysis paper, public on Oct. 25, 2023. The iLeakage vulnerability has not but been exploited within the wild as of October 27.
Bounce to:
How does the iLeakage vulnerability work?
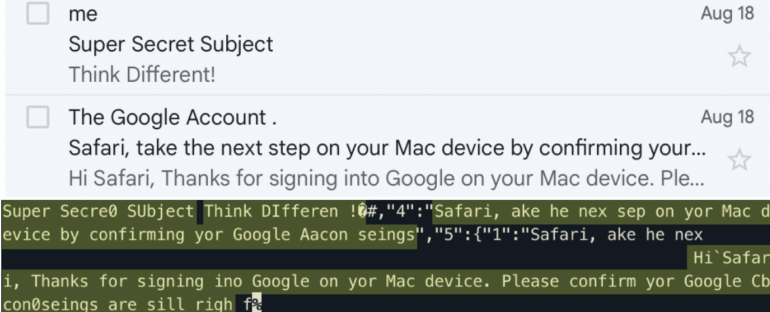
The iLeakage takes benefit of a transient execution facet channel, which is a efficiency optimization function of contemporary CPUs. The actual facet channel concerned right here is speculative execution, which could be susceptible to a {hardware} hack generally known as Spectre. Attackers can detect traces of speculative execution in CPUs, notably the cache. Attackers can power the CPU to speculatively execute the mistaken move of directions. Then, the attackers can learn delicate information contained within the ensuing facet channel (Determine A).
Determine A
The researchers who found the vulnerability are Jason Kim and Daniel Genkin of the Georgia Institute of Know-how, Stephan van Schaik of the College of Michigan and Yuval Yarom of Ruhr College Bochum.
“Code working in a single internet browser tab ought to be remoted and never be capable to infer something about different tabs {that a} consumer has open,” the researchers wrote on their web site about iLeakage. “Nonetheless, with iLeakage, malicious JavaScript and WebAssembly can learn the content material of a goal webpage when a goal visits and clicks on an attacker’s webpage. This content material consists of private info, passwords or bank card info.”
The researchers demonstrated iLeakage by establishing a web site that opens up a hidden window on the goal’s machine.
Should-read safety protection
The researchers speculate that this vulnerability has not been discovered within the wild as a result of it’s tough to orchestrate, requiring detailed information of Safari and of browser-based facet channel assaults. Nonetheless, iLeakage is essential to learn about due to its novel strategy and since the variety of units probably open to exploitation by means of iLeakage is so excessive.
TechRepublic has reached out to the researchers for extra info.
SEE: Every part you have to learn about Apple’s iOS 17 (TechRepublic)
defend towards iLeakage on Apple units
Apple has enabled a mitigation for iLeakage in macOS Ventura 13.0 and newer releases, nevertheless it takes some work to seek out it. To activate the mitigation, observe the directions posted on the iLeakage website underneath “How can I defend towards iLeakage?” to entry Safari’s debugging menu. From there, yow will discover WebKit’s inner options and an choice to disable swap processes on cross-site window openings, which prevents the iLeakage exploit from working.
Additionally, coming into Lockdown Mode or disabling JavaScript prevents the iLeakage exploit from working, however doing so could trigger a few of Safari’s options to not work.
iLeakage could be onerous to hint as a result of it doesn’t seem within the system’s log information, the researchers stated; as an alternative, iLeakage resides completely inside Safari. Some proof of the attacker web site internet hosting iLeakage could also be seen in Safari’s browser cache of not too long ago visited pages if an assault has already taken place, the researchers stated.

























