Atomic Stealer malware advertises itself via ClearFake browser updates disguised as Google’s Chrome and Apple’s Safari.
Anti-malware software program supplier Malwarebytes has described a brand new variant of Atomic Stealer (also called AMOS), which is malware focusing on Apple customers. The brand new malware variant, distributed via the pretend browser replace supply mechanism ClearFake, advertises itself as updates for Apple’s Safari browser and Google’s Chrome browser. The malware is able to grabbing a consumer’s information and sending it to an attacker’s command and management server.
Jérôme Segura, senior director of risk intelligence at Malwarebytes, famous in his submit in regards to the assault that ClearFake is actively being up to date and that its use of good contacts specifically makes it “one of the prevalent and harmful social engineering schemes.”
“Faux browser updates have been a standard theme for Home windows customers for years, and but up till now the risk actors didn’t broaden onto MacOS in a constant method,” Segura identified.
Soar to:
Timeline of Atomic Stealer malware
Atomic Stealer was first marketed as a malware supply choice for risk actors in April 2023. Malwarebytes present in September 2023 that Atomic Stealer was focusing on Mac customers via pretend software program updates marketed on Google searches. Atomic Stealer was notably suited to grabbing passwords and Apple keychain codes used for bitcoin wallets. Atomic Stealer also can elevate bank card data.
Should-read safety protection
Whereas Atomic Stealer had been focusing on Mac customers for a while, ClearFake was traditionally used solely towards Home windows machines. That is exceptional as a result of ClearFake is among the first Home windows social campaigns made for Home windows that then expanded to not solely a unique geolocation however a unique working system. Safety researcher Randy McEoin found ClearFake in August 2023.
Safety researcher Ankit Anubhav identified on Nov. 17 that, whereas ClearFake had been seen focusing on Home windows, the Mac model is a brand new growth.
How ClearFake poses as Safari and Chrome updates
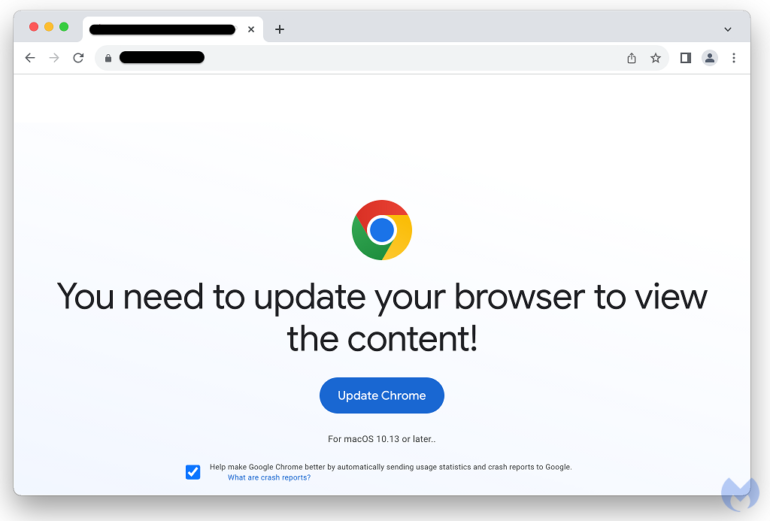
ClearFake is a sequence of malicious web sites that purport to supply updates for Safari (Determine A) and Chrome (Determine B). Potential victims will see websites posing as legit browser updates.
Determine A
Determine B
Then, the ClearFake rip-off will ship Atomic Stealer. Victims who click on via to the false updates will obtain a .dmg file that may steal passwords and extract recordsdata.
SEE: Some risk actors have used Apple gadgets for surveillance during the last yr, and it’s a development that will proceed, in line with Kaspersky. (TechRepublic)
Malwarebytes discovered that the next malicious domains are related to this risk:
Longlakeweb [dot] com
Chalomannoakhali [dot] com
Jaminzaidad [dot] cm
Royaltrustrbc [dot] com
The AMOS stealer could be recognized utilizing the next indicators:
4cb531bd83a1ebf4061c98f799cdc2922059aff1a49939d427054a556e89f464
be634e786d5d01b91f46efd63e8d71f79b423bfb2d23459e5060a9532b4dcc7b
Tips on how to defend towards this malware risk
Safety admins or IT execs ought to preserve the next in thoughts to guard staff from ClearFake and Atomic Stealer:
Preserve your group’s net safety instruments updated.
Remind staff to not obtain functions from untrusted websites. Mac customers ought to obtain functions solely from the Mac App Retailer or company-approved areas.
Talk clearly about anticipated browser updates and different software updates.




















/cdn.vox-cdn.com/uploads/chorus_asset/file/25661290/Screenshot_2024_10_06_at_10.48.36_AM.png)




