BCC (BPF Compiler Assortment) is a robust set of acceptable instruments and instance recordsdata for creating resourceful kernel tracing and manipulation packages.
It makes use of prolonged BPF (Berkeley Packet Filters), initially generally known as eBPF which was one of many new options in Linux 3.15.
Virtually, a lot of the elements utilized by BCC require Linux 4.1 or above, and its noteworthy options embody:
Requires no third celebration kernel module, since all of the instruments work primarily based on BPF which is constructed into the kernel, and BCC makes use of options added in Linux 4.x sequence.
Allows remark of software program execution.
Contains of a number of efficiency evaluation instruments with instance recordsdata and man pages.
Greatest suited to superior Linux customers, BCC makes it simple to write down BPF packages utilizing kernel instrumentation in C, and front-ends in Python and lua.
Moreover, it helps a number of duties reminiscent of efficiency evaluation, monitoring, community visitors management plus tons extra.
How To Set up BCC in Linux Programs
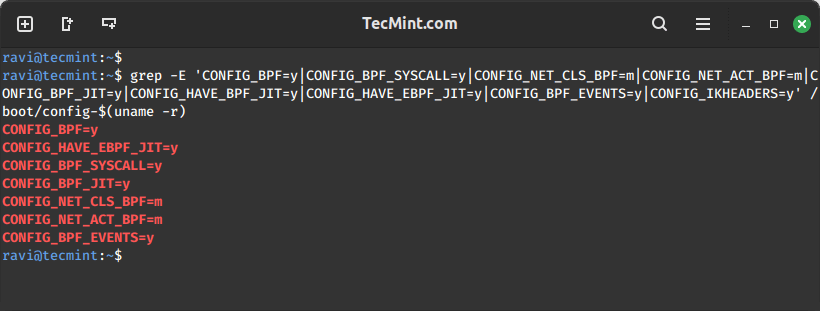
Do not forget that BCC makes use of options added in Linux kernel model 4.1 or above, and as a requirement, the kernel ought to have been compiled with the flags set beneath:
CONFIG_BPF=y
CONFIG_BPF_SYSCALL=y
# [optional, for tc filters]
CONFIG_NET_CLS_BPF=m
# [optional, for tc actions]
CONFIG_NET_ACT_BPF=m
CONFIG_BPF_JIT=y
# [for Linux kernel versions 4.1 through 4.6]
CONFIG_HAVE_BPF_JIT=y
# [for Linux kernel versions 4.7 and later]
CONFIG_HAVE_EBPF_JIT=y
# [optional, for kprobes]
CONFIG_BPF_EVENTS=y
# Want kernel headers by /sys/kernel/kheaders.tar.xz
CONFIG_IKHEADERS=y
You may verify all the desired kernel configuration flags with a single grep command and supply all of the flag names as patterns.
grep -E ‘CONFIG_BPF=y|CONFIG_BPF_SYSCALL=y|CONFIG_NET_CLS_BPF=m|CONFIG_NET_ACT_BPF=m|CONFIG_BPF_JIT=y|CONFIG_HAVE_BPF_JIT=y|CONFIG_HAVE_EBPF_JIT=y|CONFIG_BPF_EVENTS=y|CONFIG_IKHEADERS=y’ /boot/config-$(uname -r)
After verifying kernel flags, it’s time to put in BCC instruments in Linux methods.
Set up BCC Instruments on Debian
You could find bcc and its instruments within the common Debian principal repository. They arrive from the supply bundle bpfcc and are named bpfcc-tools, python3-bpfcc, libbpfcc, and libbpfcc-dev.
echo deb http://cloudfront.debian.internet/debian sid principal >> /and many others/apt/sources.listing
sudo apt-get set up -y bpfcc-tools libbpfcc libbpfcc-dev linux-headers-$(uname -r)
Set up BCC Instruments on Ubuntu
You could find totally different variations of bcc within the common Ubuntu Universe repository.
sudo apt-get set up bpfcc-tools linux-headers-$(uname -r)
Set up BCC Instruments on Fedora
As of Fedora 40, bcc binaries can be found in the usual repository.
sudo dnf set up bcc
Set up BCC Instruments on RHEL
bcc is already included within the official yum repository as bcc-tools.
sudo yum set up bcc-tools
Set up BCC Instruments on Arch Linux
bcc is offered in the usual Arch repository and will be put in with the pacman command.
pacman -S bcc bcc-tools python-bcc
Set up BCC Instruments on openSUSE
For openSUSE Leap 42.2 (and later) and Tumbleweed, bcc is already included within the official repo.
sudo zypper ref
sudo zypper in bcc-tools bcc-examples
How To Use BCC Instruments in Linux Programs
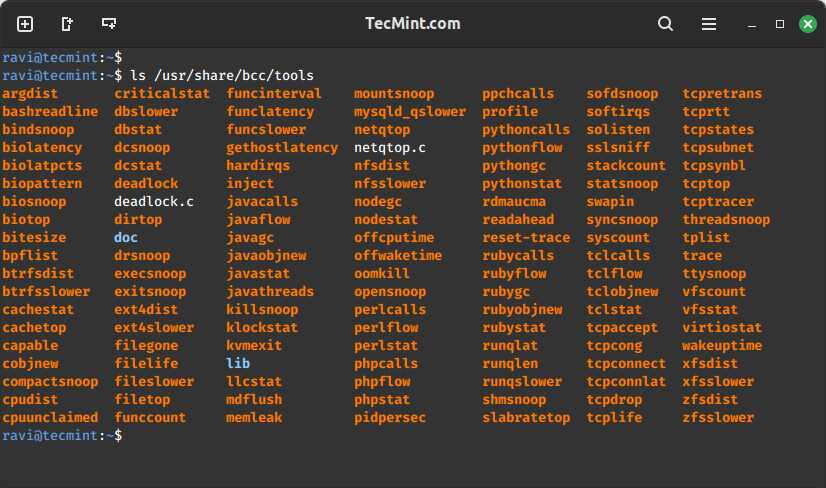
All of the BCC instruments are put in beneath /usr/share/bcc/instruments listing. Nonetheless, you possibly can alternatively run them from the BCC Github repository beneath /instruments the place they finish with an .py extension.
ls /usr/share/bcc/instruments
We will cowl just a few examples of – monitoring normal Linux system efficiency and networking.
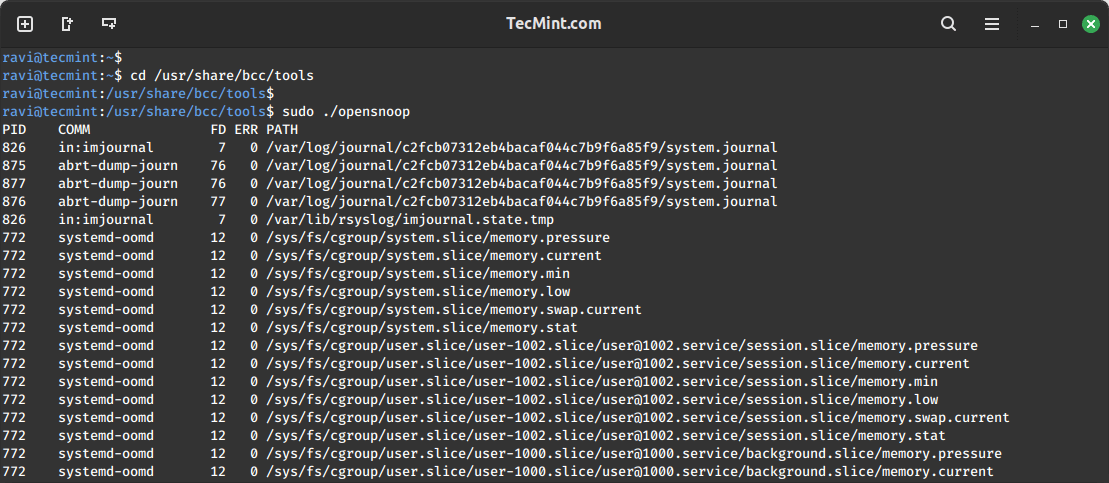
Tracing open() Syscalls in Linux
Let’s begin by tracing all open() syscalls utilizing opensnoop software. This permits us to inform how numerous purposes work by figuring out their information recordsdata, config recordsdata, and lots of extra:
cd /usr/share/bcc/instruments
sudo ./opensnoop
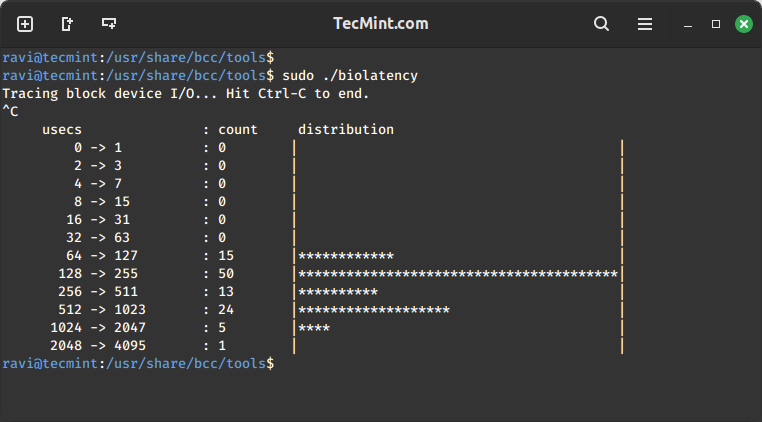
Analyzing Disk I/O Latency in Linux
This instance exhibits a summarized distribution of disk I/O latency utilizing biolatency software. After executing the command, watch for a couple of minutes and hit Ctrl-C to finish it and look at the output.
sudo ./biolatency
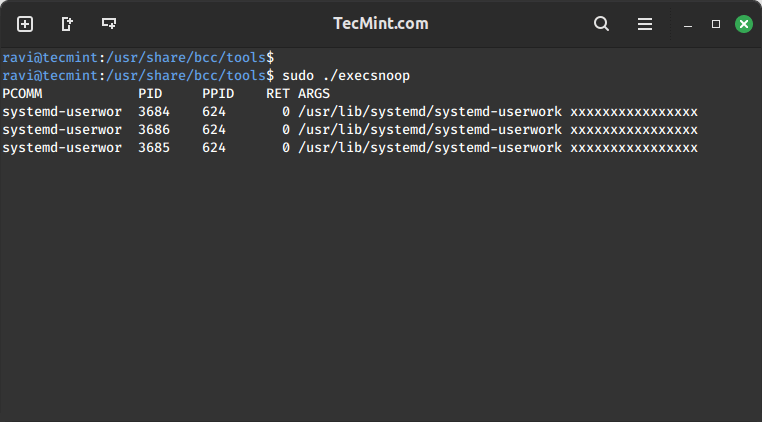
Tracing New Processes in Linux
On this part, we will transfer to tracing new processes in execution utilizing execsnoop software. Every time a course of is forked by fork() and exec() syscalls, it’s proven within the output. Nonetheless, not all processes are captured.
sudo ./execsnoop
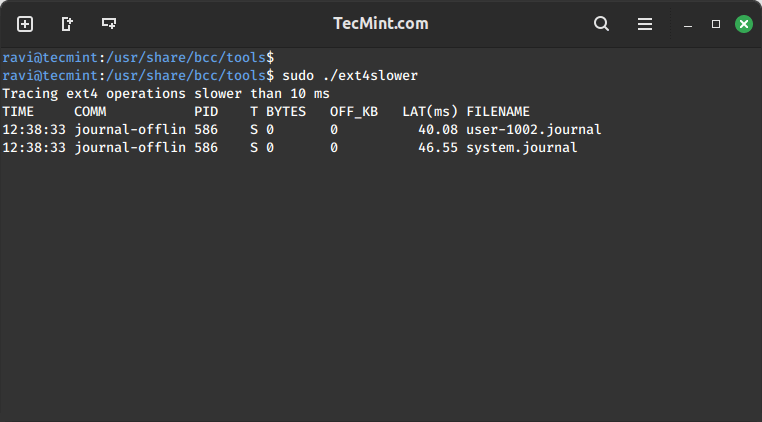
Hint Slower Ext4 File System Operations
Utilizing ext4slower to hint the ext4 file system frequent operations which might be slower than 10ms, to assist us establish independently gradual disk I/O by way of the file system.
It solely outputs these operations that exceed a threshold:
sudo ./ext4slower
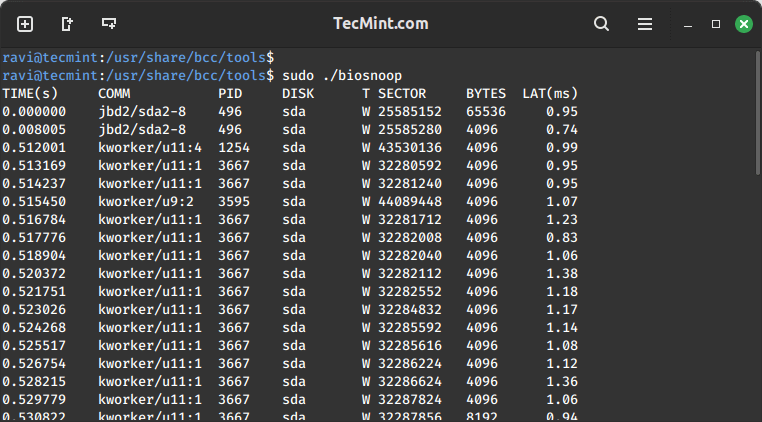
Exploring Disk I/O Exercise with biosnoop
Subsequent off, let’s dive into printing a line per disk I/O every second, with particulars reminiscent of course of ID, sector, bytes, and latency amongst others utilizing biosnoop software:
sudo ./biosnoop
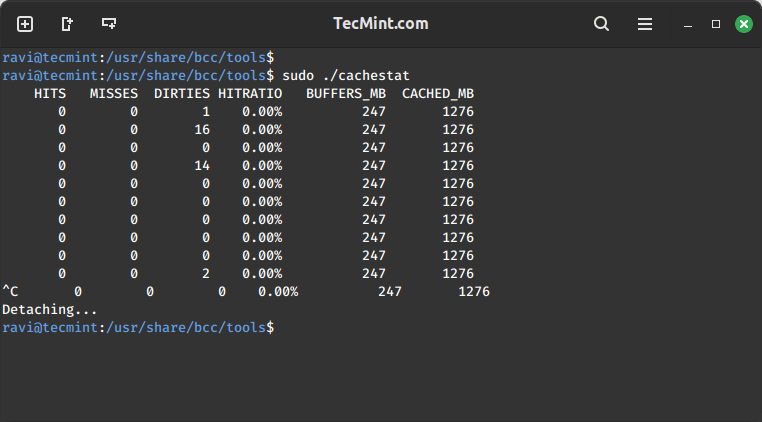
Analyzing System Cache Efficiency
Thereafter, we proceed to make use of cachestat software to show one line of summarized statistics from the system cache each second. This permits for system tuning operations by declaring low cache hit ratio and excessive price of misses:
sudo ./cachestat
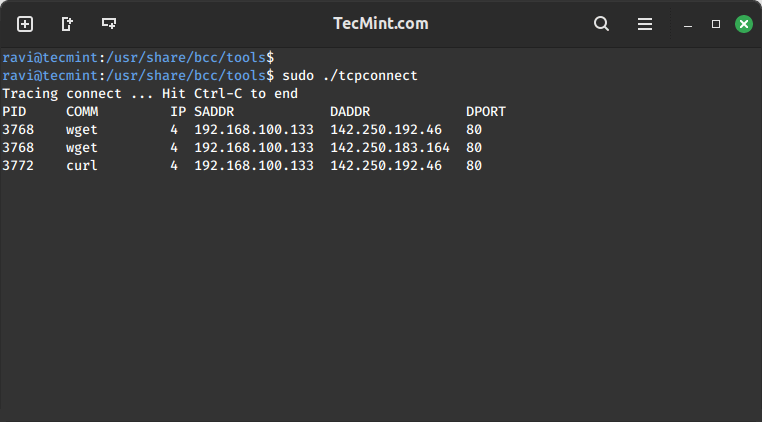
Monitoring TCP Connections in Linux
Monitoring TCP connections each second utilizing tcpconnect software. Its output contains supply and vacation spot handle, and port quantity. This software is helpful for tracing surprising TCP connections, thereby serving to us to establish inefficiencies in software configurations or an attacker.
sudo ./tcpconnect
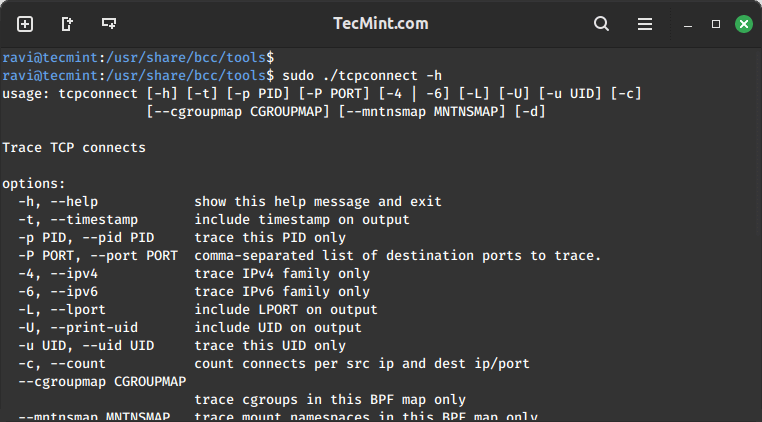
All of the instruments above may also be used with numerous choices, to allow the assistance web page for a given software, make use of the -h choice, for instance:
sudo ./tcpconnect -h
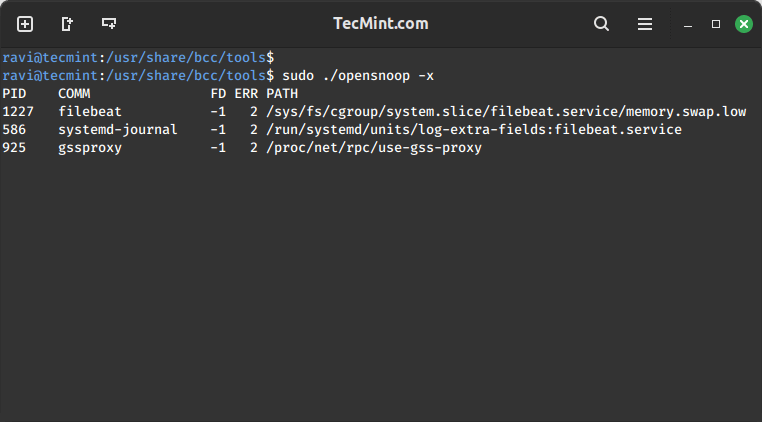
Hint Failed exec()s Syscalls
To hint failed exec()s syscalls, make use of the -x choice with opensnoop as beneath:
sudo ./opensnoop -x
Hint Explicit Course of Capabilities
The final instance beneath demonstrates execute a customized hint operation. We’re tracing a specific course of utilizing its PID.
First, decide the method ID:
pidof firefox
In a while, run the customized hint command. The command beneath -p specifies the method ID, do_sys_open() is a kernel operate that’s traced dynamically together with its second argument as a string.
sudo ./hint -p 4095 ‘do_sys_open “%s”, arg2’
Abstract
BCC is a robust and easy-to-use toolkit for numerous system administration duties reminiscent of tracing system efficiency monitoring, tracing block gadget I/O, TCP capabilities, file system operations, syscalls, Node.js probes, plus tons extra. Importantly, it ships with a number of instance recordsdata and man pages for the instruments to information you, making it person pleasant and dependable.
Final however not least, you will get again to us by sharing your ideas concerning the topic, asking questions, making helpful recommendations, or any constructive suggestions by way of the remark part beneath.




![[SOLVED] ShareFile for Outlook Has Fired an Exception Error [SOLVED] ShareFile for Outlook Has Fired an Exception Error](https://mspoweruser.com/wp-content/uploads/2024/07/sharefile-for-outlook-has-fired-an-exception.png)