The Cisco Talos report exposes new malware utilized by the group to focus on Web spine infrastructure and healthcare organizations within the U.Okay. and the U.S.
Two studies from cybersecurity firm Cisco Talos present intelligence a couple of new assault marketing campaign from the North Korean risk actor Lazarus. The studies expose new malware and instruments utilized by the group, which retains utilizing the identical infrastructure.
Soar to:
What is that this new malware assault chain?
The researchers noticed the Lazarus group efficiently compromise an web spine infrastructure supplier within the U.Okay. in early 2023, deploying a brand new malware dubbed QuiteRAT.
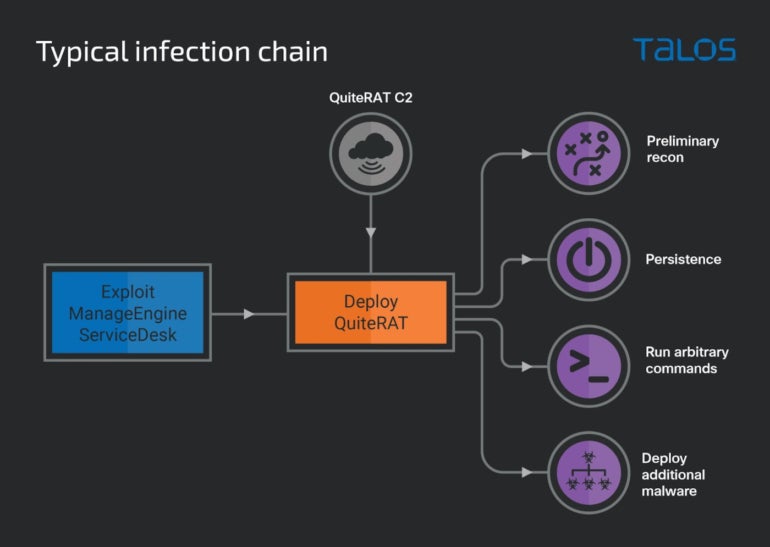
The preliminary compromise was accomplished by way of exploitation of the CVE-2022-47966 vulnerability, which impacts Zoho’s ManageEngine ServiceDesk. The risk actor leveraged an exploit for it 5 days after the proof of idea was publicly disclosed. The profitable exploit downloaded and executed the QuiteRAT malware, hosted on an IP handle utilized by Lazarus since no less than Might 2022.
As soon as the malware has been executed, it begins sending preliminary details about the system to its command-and-control server and waits for a solution, which could be a direct command to the malware or a Microsoft Home windows command line to be executed by way of the cmd.exe course of. The preliminary info is being encrypted and despatched to the C2; it consists of community configuration info (i.e., IP handle and MAC handle) and the presently logged in person title (Determine A).
Determine A
The Lazarus group’s new arsenal of malware
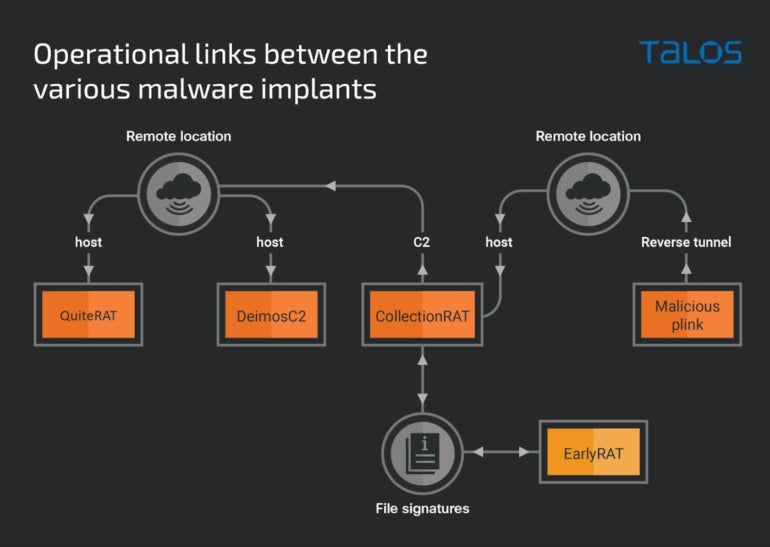
Lazarus has used varied malware on this assault marketing campaign: QuiteRAT, CollectionRAT, DeimosC2 and malicious Plink.
QuiteRAT
QuiteRAT is a distant entry device largely constructed utilizing Qt libraries and developer code. Using Qt for writing malware is uncommon as a result of this framework is normally used to develop graphical person interfaces. Qt use makes the code extra advanced to investigate for reverse engineers, and would possibly render machine studying and heuristic detections by safety options much less dependable as a result of they won’t flag using the Qt libraries as malicious.
It’s not the primary time Lazarus has used the Qt framework for growing malware. MagicRAT malware was already utilizing it, and similarities between each (e.g., having the identical skills, the identical encoding scheme and related performance to permit them to stay dormant) point out that QuiteRAT has been derived from MagicRAT. Moreover, Cisco Talos notes that the final MagicRAT model they noticed was compiled in April 2022, whereas the QuiteRAT samples they discovered had been compiled in Might and July 2022. This would possibly point out a change from MagicRAT to QuiteRAT, which is smaller and extra compact: MagicRAT takes 18MB, whereas QuiteRAT is round 4MB to 5MB.
CollectionRAT
CollectionRAT is one other RAT used and possibly developed by Lazarus. The malware is a packed Microsoft Basis Class library-based Home windows binary that decrypts and executes the precise malware code on the fly. The malware gathers info from the system it contaminated and offers totally different standard features for a RAT: it permits knowledge assortment, can present a reverse shell to run arbitrary instructions on the system, learn and write on the disk, and obtain and execute extra payloads.
Should-read safety protection
The researchers discovered info that may point out CollectionRAT has spawned from one other malware household generally known as EarlyRAT, which is attributed to the Andariel subgroup of Lazarus. One CollectionRAT pattern used the very same code-signing certificates as an older model of EarlyRAT from 2021.
DeimosC2
DeimosC2 is an open-source post-exploitation C2 device that leverages a number of communication strategies with the intention to management machines which have been compromised. It’s utilized by Lazarus as a method of preliminary and protracted entry.
The researchers discovered a Linux DeimosC2 implant on the infrastructure, indicating the risk actor deliberate to deploy it throughout the preliminary entry to compromised Linux-based servers. The implant was not closely custom-made, which could be a sign that Lazarus remains to be within the technique of testing it or getting used to it.
The implants sometimes have varied RAT capabilities, resembling executing instructions, stealing credentials, downloading and executing extra payloads.
Malicious Plink
Plink, often known as PuTTY Hyperlink, is a professional open-source device utilized by community directors to get reverse tunneling functionality when wanted. Lazarus used the device as-is up to now, however the group has began to switch the supply code of it to embed the reverse tunnel command strings within the binary itself.
Lazarus retains reusing the identical infrastructure
Though the group makes plenty of adjustments to its arsenal, the North Korean state-sponsored Lazarus risk actor “continues to make use of a lot of the identical infrastructure regardless of these parts being well-documented by safety researchers through the years,” in keeping with Cisco Talos. That is excellent news for safety as a result of it permits IT workers and researchers to trace the risk actor extra simply and shield in opposition to it. But it may additionally imply that Lazarus is assured sufficient of their operations and don’t assume it’s needed to vary a lot of their assault infrastructure.
QuiteRAT has been present in the identical distant location as DeimosC2 brokers and MagicRAT malware utilized in 2022 by Lazarus. The situation has additionally been used for CollectionRAT.
The totally different instruments and malware utilized by Lazarus can all be tied collectively utilizing the infrastructure (Determine B).
Determine B
Tips on how to shield your small business from this safety risk
On this assault marketing campaign, the preliminary compromise was accomplished by exploiting a vulnerability affecting Zoho’s ManageEngine ServiceDesk that was patched round November 2022. Suggestions for safeguarding from this safety risk embrace:
Maintain software program and working programs updated and patched.
Monitor networks with safety options.
Make guidelines to detect the communications from the malware uncovered on this assault marketing campaign.
Monitor IP addresses utilized by the risk actor.
Deploy safety options on endpoints and servers with the intention to detect malware and instruments that could be used to assault your group. These options must also monitor the e-mail contents, hooked up recordsdata and attainable hyperlinks to malicious content material.
Disclosure: I work for Development Micro, however the views expressed on this article are mine.

























