Final week, the US joined the U.Ok. and Australia in sanctioning and charging a Russian man named Dmitry Yuryevich Khoroshev because the chief of the notorious LockBit ransomware group. LockBit’s chief “LockBitSupp” claims the feds named the flawed man, saying the fees don’t clarify how they linked him to Khoroshev. This put up examines the actions of Khoroshev’s many alter egos on the cybercrime boards, and tracks the profession of a gifted malware creator who has written and offered malicious code for the previous 14 years.
Dmitry Yuryevich Khoroshev. Picture: treasury.gov.
On Could 7, the U.S. Division of Justice indicted Khoroshev on 26 legal counts, together with extortion, wire fraud, and conspiracy. The federal government alleges Khoroshev created, offered and used the LockBit ransomware pressure to personally extort greater than $100 million from lots of of sufferer organizations, and that LockBit as a bunch extorted roughly half a billion {dollars} over 4 years.
Federal investigators say Khoroshev ran LockBit as a “ransomware-as-a-service” operation, whereby he saved 20 p.c of any ransom quantity paid by a sufferer group contaminated along with his code, with the remaining 80 p.c of the cost going to LockBit associates liable for spreading the malware.
Monetary sanctions levied in opposition to Khoroshev by the U.S. Division of the Treasury listed his identified e mail and road tackle (in Voronezh, in southwest Russia), passport quantity, and even his tax ID quantity (hey, Russian tax authorities). The Treasury submitting says Khoroshev used the emails sitedev5@yandex.ru, and khoroshev1@icloud.com.
In line with DomainTools.com, the tackle sitedev5@yandex.ru was used to register a minimum of six domains, together with a Russian enterprise registered in Khoroshev’s title referred to as tkaner.com, which is a weblog about clothes and materials.
A search on the breach-tracking service Constella Intelligence on the cellphone quantity in Tkaner’s registration data — 7.9521020220 — brings up a number of official Russian authorities paperwork itemizing the quantity’s proprietor as Dmitri Yurievich Khoroshev.
One other area registered to that cellphone quantity was stairwell[.]ru, which at one level marketed the sale of wood staircases. Constella finds that the e-mail addresses webmaster@stairwell.ru and admin@stairwell.ru used the password 225948.
DomainTools experiences that stairwell.ru for a number of years included the registrant’s title as “Dmitrij Ju Horoshev,” and the e-mail tackle pin@darktower.su. In line with Constella, this e mail tackle was utilized in 2010 to register an account for a Dmitry Yurievich Khoroshev from Voronezh, Russia on the internet hosting supplier firstvds.ru.

Picture: Shutterstock.
Cyber intelligence agency Intel 471 finds that pin@darktower.ru was utilized by a Russian-speaking member referred to as Pin on the English-language cybercrime discussion board Opensc. Pin was lively on Opensc round March 2012, and authored 13 posts that principally involved knowledge encryption points, or easy methods to repair bugs in code.
Different posts involved {custom} code Pin claimed to have written that may bypass reminiscence protections on Home windows XP and Home windows 7 methods, and inject malware into reminiscence house usually allotted to trusted functions on a Home windows machine.
Pin additionally was lively at that very same time on the Russian-language safety discussion board Antichat, the place they instructed fellow discussion board members to contact them on the ICQ instantaneous messenger quantity 669316.
NEROWOLFE
A search on the ICQ quantity 669316 at Intel 471 reveals that in April 2011, a person by the title NeroWolfe joined the Russian cybercrime discussion board Zloy utilizing the e-mail tackle d.horoshev@gmail.com, and from an Web tackle in Voronezh, RU.
Constella finds the identical password tied to webmaster@stairwell.ru (225948) was utilized by the e-mail tackle 3k@xakep.ru, which Intel 471 says was registered to greater than a dozen NeroWolfe accounts throughout simply as many Russian cybercrime boards between 2011 and 2015.
NeroWolfe’s introductory put up to the discussion board Verified in Oct. 2011 stated he was a system administrator and C++ coder.
“Putting in SpyEYE, ZeuS, any DDoS and spam admin panels,” NeroWolfe wrote. This person stated they specialise in growing malware, creating laptop worms, and crafting new methods to hijack Internet browsers.

“I can present my portfolio on request,” NeroWolfe wrote. “P.S. I don’t modify another person’s code or work with another person’s frameworks.”
In April 2013, NeroWolfe wrote in a personal message to a different Verified discussion board person that he was promoting a malware “loader” program that would bypass all the safety protections on Home windows XP and Home windows 7.
“The entry to the community is barely restricted,” NeroWolfe stated of the loader, which he was promoting for $5,000. “You gained’t handle to bind a port. Nevertheless, it’s fairly doable to ship knowledge. The code is written in C.”
In an October 2013 dialogue on the cybercrime discussion board Exploit, NeroWolfe weighed in on the karmic ramifications of ransomware. On the time, ransomware-as-a-service didn’t exist but, and lots of members of Exploit had been nonetheless making good cash from “lockers,” comparatively crude packages that locked the person out of their system till they agreed to make a small cost (normally a number of hundred {dollars} through pay as you go Inexperienced Dot playing cards).
Lockers, which presaged the approaching ransomware scourge, had been typically seen by the Russian-speaking cybercrime boards as innocent moneymaking alternatives, as a result of they normally didn’t search to hurt the host laptop or endanger information on the system. Additionally, there have been nonetheless loads of locker packages that aspiring cybercriminals may both purchase or hire to make a gradual earnings.
NeroWolfe reminded discussion board denizens that they had been simply as susceptible to ransomware assaults as their would-be victims, and that what goes round comes round.
“Guys, do you have got a conscience?,” NeroWolfe wrote. “Okay, lockers, community gopstop aka enterprise in Russian. The very last thing was all the time squeezed out of the suckers. However encoders, nobody is protected against them, together with the native viewers.”
If Khoroshev was ever frightened that somebody outdoors of Russia may be capable of join his early hacker handles to his actual life persona, that’s not clear from reviewing his historical past on-line. In actual fact, the identical e mail tackle tied to so a lot of NeroWolfe’s accounts on the boards — 3k@xakep.ru — was utilized in 2011 to create an account for a Dmitry Yurevich Khoroshev on the Russian social media community Vkontakte.
NeroWolfe appears to have deserted all of his discussion board accounts someday in 2016. In November 2016, an exploit[.]ru member filed an official grievance in opposition to NeroWolfe, saying NeroWolfe had been paid $2,000 to provide {custom} code however by no means completed the mission and vanished.
It’s unclear what occurred to NeroWolfe or to Khoroshev throughout this time. Possibly he received arrested, or some shut associates did. Maybe he simply determined it was time to put low and hit the reset on his operational safety efforts, given his previous failures on this regard. It’s additionally doable NeroWolfe landed an actual job someplace for a number of years, fathered a toddler, and/or needed to put his cybercrime profession on maintain.
PUTINKRAB
Or maybe Khoroshev noticed the approaching ransomware business for the infinite pot of gold that it was about to grow to be, after which devoted himself to engaged on {custom} ransomware code. That’s what the federal government believes.
The indictment in opposition to Khoroshev says he used the hacker nickname Putinkrab, and Intel 471 says this corresponds to a username that was first registered throughout three main Russian cybercrime boards in early 2019.
KrebsOnSecurity may discover no apparent connections between Putinkrab and any of Khoroshev’s older identities. Nevertheless, if Putinkrab was Khoroshev, he would have realized from his previous errors and began contemporary with a brand new id (which he did). But in addition, it’s probably the federal government hasn’t shared all the intelligence it has collected in opposition to him (extra on that in a bit).
Putinkrab’s first posts on the Russian cybercrime boards XSS, Exploit and UFOLabs noticed this person promoting ransomware supply code written in C.
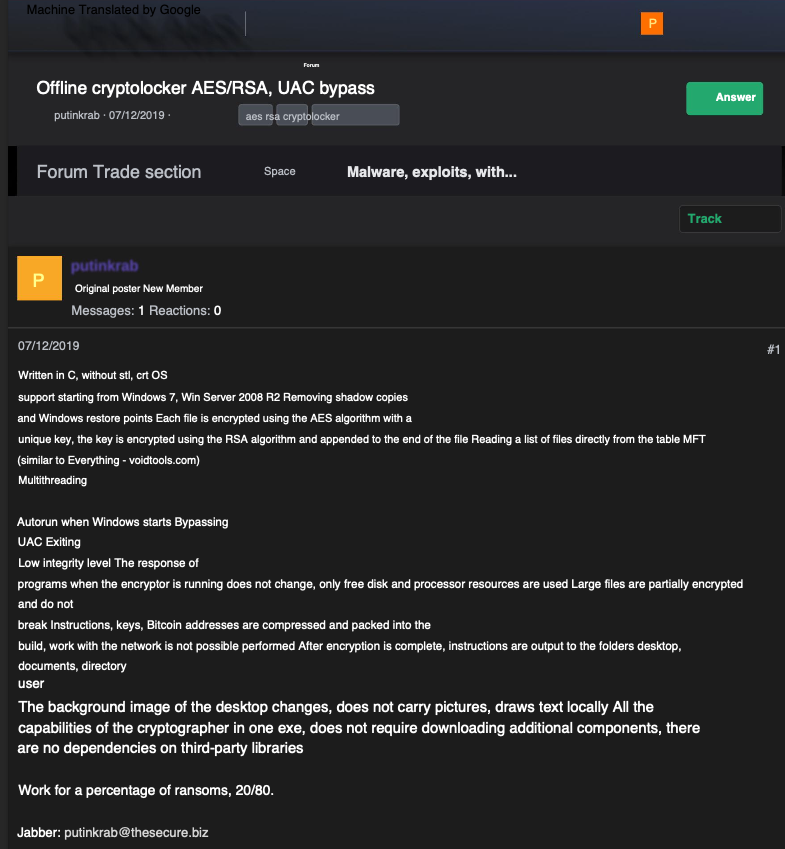
A machine-translated advert for ransomware supply code from Putinkrab on the Russian language cybercrime discussion board UFOlabs in 2019. Picture: Ke-la.com.
In April 2019, Putkinkrab provided an associates program that may run on prime of his custom-made ransomware code.
“I wish to work for a share of the ransoms: 20/80,” Putinkrab wrote on Exploit. “20 p.c is my share for the work, you get 80% of the ransoms. The share may be lowered as much as 10/90 if the volumes are good. However now, quickly, till the service is totally automated, we’re working utilizing a unique algorithm.”
All through the summer season of 2019, Putinkrab posted a number of updates to Exploit about new options being added to his ransomware pressure, in addition to novel evasion strategies to keep away from detection by safety instruments. He additionally instructed discussion board members he was on the lookout for buyers for a brand new ransomware mission based mostly on his code.
In response to an Exploit member who complained that the safety business was making it more durable to revenue from ransomware, Putinkrab stated that was as a result of so many cybercriminals had been counting on crappy ransomware code.
“The overwhelming majority of prime antiviruses have acquired behavioral evaluation, which blocks 95% of crypto-lockers at their root,” Putinkrab wrote. “Cryptolockers made a whole lot of noise within the press, however lazy system directors don’t make backups after that. The overwhelming majority of cryptolockers are written by individuals who have little understanding of cryptography. Due to this fact, decryptors seem on the Web, and with them the hope that information may be decrypted with out paying a ransom. They simply sit and wait. Contact with the proprietor of the hot button is misplaced over time.”
Putinkrab stated he had each confidence his ransomware code was a game-changer, and an enormous cash machine.
“The sport is simply gaining momentum,” Putinkrab wrote. “Weak gamers lose and are eradicated.”
The remainder of his response was structured like a poem:
“On this world, the strongest survive.Our life is only a wrestle.The winner would be the smartest,Who has his head on his shoulders.”
Putinkrab’s last put up got here on August 23, 2019. The Justice Division says the LockBit ransomware associates program was formally launched 5 months later. From there on out, the federal government says, Khoroshev adopted the persona of LockBitSupp. In his introductory put up on Exploit, LockBit’s mastermind stated the ransomware pressure had been in growth since September 2019.
The unique LockBit malware was written in C (a language that NeroWolfe excelled at). Right here’s the unique description of LockBit, from its maker:
“The software program is written in C and Assembler; encryption is carried out by way of the I/O Completion Port; there’s a port scanning native networks and an choice to search out all DFS, SMB, WebDAV community shares, an admin panel in Tor, automated check decryption; a decryption instrument is supplied; there’s a chat with Push notifications, a Jabber bot that forwards correspondence and an choice to terminate providers/processes in line which stop the ransomware from opening information at a sure second. The ransomware units file permissions and removes blocking attributes, deletes shadow copies, clears logs and mounts hidden partitions; there may be an choice to drag-and-drop information/folders and a console/hidden mode. The ransomware encrypts information in elements in varied locations: the bigger the file dimension, the extra elements there are. The algorithms used are AES + RSA.
You’re the one who determines the ransom quantity after speaking with the sufferer. The ransom paid in any forex that fits you may be transferred to your wallets. The Jabber bot serves as an admin panel and is used for banning, offering decryption instruments, chatting – Jabber is used for completely all the things.”
CONCLUSION
Does the above timeline show that NeroWolfe/Khoroshev is LockBitSupp? No. Nevertheless, it does point out Khoroshev was for a few years deeply invested in numerous schemes involving botnets, stolen knowledge, and malware he wrote that others used to nice impact. NeroWolfe’s many non-public messages from fellow discussion board members affirm this.
NeroWolfe’s specialty was creating {custom} code that employed novel stealth and evasion strategies, and he was all the time fast to volunteer his providers on the boards each time anybody was trying assistance on a malware mission that referred to as for a powerful C or C++ programmer.
Somebody with these {qualifications} — in addition to demonstrated mastery of knowledge encryption and decryption strategies — would have been in nice demand by the ransomware-as-a-service business that took off at across the identical time NeroWolfe vanished from the boards.
Somebody like that who’s close to or on the prime of their recreation vis-a-vis their friends doesn’t merely stroll away from that stage of affect, group standing, and potential earnings stream except compelled to take action by circumstances past their quick management.
It’s vital to notice that Putinkrab didn’t simply materialize out of skinny air in 2019 — out of the blue endowed with data about easy methods to write superior, stealthy ransomware strains. That data clearly got here from somebody who’d already had years of expertise constructing and deploying ransomware strains in opposition to real-life sufferer organizations.
Thus, whoever Putinkrab was earlier than they adopted that moniker, it’s a secure guess they had been concerned within the growth and use of earlier, extremely profitable ransomware strains. One sturdy doable candidate is Cerber ransomware, the preferred and efficient associates program working between early 2016 and mid-2017. Cerber thrived as a result of it emerged as an early mover out there for ransomware-as-a-service choices.
In February 2024, the FBI seized LockBit’s cybercrime infrastructure on the darkish net, following an apparently prolonged infiltration of the group’s operations. The US has already indicted and sanctioned a minimum of 5 different alleged LockBit ringleaders or associates, so presumably the feds have been in a position to attract extra sources from these investigations.
Additionally, it appears probably that the three nationwide intelligence businesses concerned in bringing these fees are usually not displaying all of their playing cards. For instance, the Treasury paperwork on Khoroshev point out a single cryptocurrency tackle, and but specialists interviewed for this story say there aren’t any apparent clues connecting this tackle to Khoroshev or Putinkrab.
However provided that LockBitSupp has been actively concerned in Lockbit ransomware assaults in opposition to organizations for 4 years now, the federal government virtually actually has an intensive checklist of the LockBit chief’s varied cryptocurrency addresses — and doubtless even his financial institution accounts in Russia. And little question the cash path from a few of these transactions was traceable to its final beneficiary (or shut sufficient).
Not lengthy after Khoroshev was charged because the chief of LockBit, a lot of open-source intelligence accounts on Telegram started extending the knowledge launched by the Treasury Division. Inside hours, these sleuths had unearthed greater than a dozen bank card accounts utilized by Khoroshev over the previous decade, in addition to his varied checking account numbers in Russia.
The purpose is, this put up is predicated on knowledge that’s obtainable to and verifiable by KrebsOnSecurity. Woodward & Bernstein’s supply within the Watergate investigation — Deep Throat — famously instructed the 2 reporters to “comply with the cash.” That is all the time wonderful recommendation. However lately, that may be loads simpler stated than executed — particularly with individuals who a) don’t want to be discovered, and b) don’t precisely file annual experiences.


























