Microsoft on Tuesday launched 79 patches touching eleven product households. Seven of these points, affecting Azure, SharePoint, and Home windows, are thought-about by Microsoft to be of important severity. At press time, three of the problems addressed are identified to be below exploit within the wild, with a fourth concern not itself below exploit, however intertwined with points which are. (For particulars on this uncommon scenario, please see the “Notable September updates” part beneath.) Microsoft assesses that 11 CVEs, all in Home windows, are by the corporate’s estimation extra prone to be exploited within the subsequent 30 days. Eight of this month’s points are amenable to detection by Sophos protections, and we embody data on these in a desk beneath.
Along with these patches, the discharge consists of advisory data on three CVEs addressed by patches from Adobe, affecting Reader and ColdFusion; one of many Reader vulnerabilities CVE-2024-41869) is a critical-severity use-after-free with a workable exploit already accessible within the wild. We’re as at all times together with on the finish of this put up further appendices itemizing all Microsoft’s patches, sorted by severity, by predicted exploitability, and by product household.
By the numbers
Complete CVEs: 79
Complete Adobe advisories lined in replace: 3
Publicly disclosed: 1
Exploited detected: 4*
Severity
Vital: 7
Vital: 71
Reasonable: 1
Impression
Elevation of privilege: 30
Distant code execution: 23
Info disclosure: 11
Denial of service: 8
Safety function bypass: 4
Spoofing: 3
CVSS base rating 9.0 or larger: 2
CVSS base rating 8.0 or larger: 24
* For data on why we depend CVE-2024-43491 as this month’s fourth exploited-detected CVE regardless of the CVE itself not being detected as below exploit, please see the “Notable September updates” part beneath.
Determine 1: This month’s critical-severity patches embody one for which exploitation has already been detected, and two extra for which exploitation is extra possible throughout the subsequent 30 days
Product households
Home windows: 47
SQL Server: 13
Azure: 6
SharePoint: 5
Workplace: 4
365: 2
Dynamics 365: 2
Microsoft AutoUpdate (MAU) for Mac: 1
Outlook for iOS: 1
Energy BI: 1
Visio: 1
As is our customized for this checklist, CVEs that apply to multiple product household are counted as soon as for every household they have an effect on.
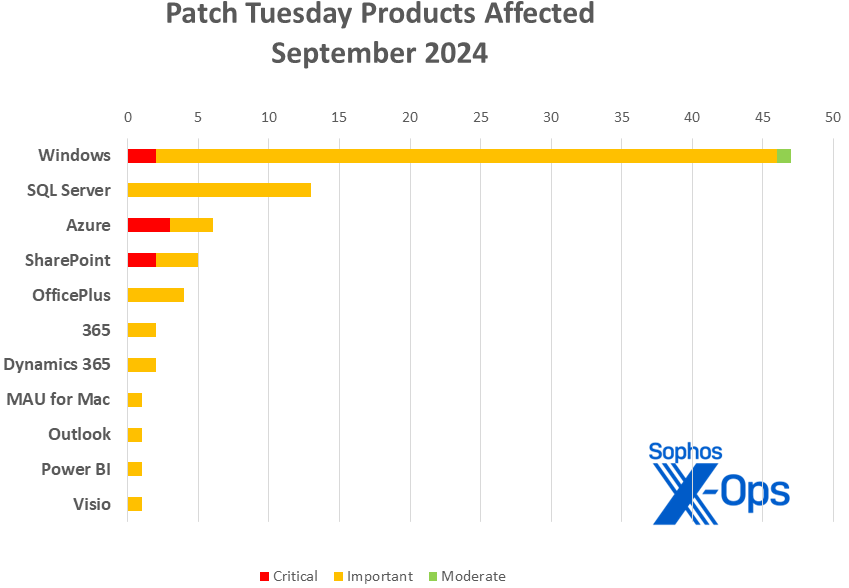
Determine 2: Although Home windows as standard leads the checklist of affected product households, a set of Native Scoring points in SQL Server contributed to that product taking 13 patches of its personal
Notable September updates
Along with the problems mentioned above, various particular gadgets advantage consideration.
CVE-2024-38217 — Home windows Mark of the Net Safety Function Bypass VulnerabilityCVE-2024-43492 — Home windows Mark of the Net Safety Function Bypass Vulnerability
There are patches for 2 Mark of the Net vulnerabilities this month, and each are both at present below lively exploit within the wild (CVE-2024-38217) or judged by Microsoft as extra prone to be exploited throughout the subsequent 30 days (CVE-2024-43492). The latter bug was discovered in-house at Microsoft and is taken into account to be of reasonable severity. The previous, nevertheless, was disclosed responsibly by Elastic Safety’s Joe Desimone, who has posted concerning the discovery and the reporting course of, and which can be of curiosity to those that comply with points round code-signing certificates. The bug impacts all variations of Home windows together with Win 11H24 and is of essential severity.
CVE-2024-38014 — Home windows Installer Elevation of Privilege Vulnerability
This concern is below lively exploit within the wild. It impacts all variations of Home windows together with Win 11H24.
CVE-2024-43491 – Microsoft Home windows Replace Distant Code Execution Vulnerability
The excellent news is that this concern impacts solely sure operational parts of Home windows 10, model 1507 (first launched in July 2015); solely two variations of that construct, Home windows 10 Enterprise 2015 LTSB and Home windows 10 IoT Enterprise 2015 LTSB, are nonetheless below help. The dangerous information, for these nonetheless working both of these variations, is that critical-severity distant code execution concern, which carries a 9.8 CVE base rating, happens in… the Home windows Servicing Stack. It’s a captivating concern for individuals who care about such issues — somewhat than a coding error per se, Microsoft explains that the construct model numbers themselves “crossed into a spread that triggered a code defect within the Home windows 10 (model 1507) servicing stack that handles the applicability of Non-compulsory Elements. In consequence, any Non-compulsory Element that was serviced with updates launched since March 12, 2024 (KB5035858) was detected as “not relevant” by the servicing stack and was reverted to its RTM model.” If this concern is relevant to your property, it is strongly recommended that you simply intently learn and comply with the knowledge Microsoft supplies in KB5043083, because the patch sequence one should comply with is exact. That web page additionally features a checklist of the particular non-compulsory parts affected, which can assist make clear your publicity.
[29 CVEs] — Home windows 11 24H2 patches
Although Home windows 11 24H2 just isn’t but basically launch, simply over a 3rd of this month’s patches have an effect on that platform, together with two (CVE-2024-38014, CVE-2024-38217) for which exploitation has already been detected within the wild. Customers of the brand new Copilot+ PCs who don’t ingest their patches mechanically ought to remember to replace their gadgets.
[0 CVEs] — .NET, Visible Studio, Edge / Chromium, non-iOS Outlook
A uncommon month of respite for .NET and Visible Studio, with no patches launched for these households. Nor are there any this time round associated to Edge, or to Outlook for platforms apart from Apple’s.
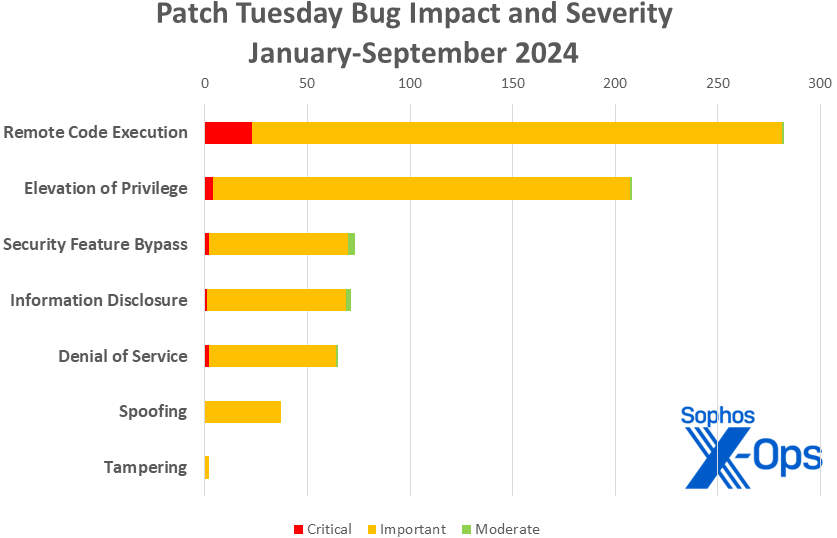
Determine 3: Regardless of the predominance of EoP points in current months, RCE continues to steer the pack as we attain the three-quarter mark for 2024.
Sophos protections
CVE
Sophos Intercept X/Endpoint IPS
Sophos XGS Firewall
CVE-2024-38237
Exp/2438237-A
Exp/2438237-A
CVE-2024-38238
Exp/2438238-A
Exp/2438238-A
CVE-2024-38241
Exp/2438241-A
Exp/2438241-A
CVE-2024-38242
Exp/2438242-A
Exp/2438242-A
CVE-2024-38243
Exp/2438243-A
Exp/2438243-A
CVE-2024-38244
Exp/2438244-A
Exp/2438244-A
CVE-2024-38245
Exp/2438245-A
Exp/2438245-A
CVE-2024-43461
SID:2310127
SID:2310126
As you possibly can each month, for those who don’t wish to wait on your system to drag down Microsoft’s updates itself, you possibly can obtain them manually from the Home windows Replace Catalog web site. Run the winver.exe device to find out which construct of Home windows 10 or 11 you’re working, then obtain the Cumulative Replace bundle on your particular system’s structure and construct quantity.
Appendix A: Vulnerability Impression and Severity
This can be a checklist of September patches sorted by impression, then sub-sorted by severity. Every checklist is additional organized by CVE.
Elevation of Privilege (30 CVEs)
Vital severity
CVE-2024-38194
Azure Net Apps Elevation of Privilege Vulnerability
CVE-2024-38216
Azure Stack Hub Elevation of Privilege Vulnerability
CVE-2024-38220
Azure Stack Hub Elevation of Privilege Vulnerability
Vital severity
CVE-2024-37341
Microsoft SQL Server Elevation of Privilege Vulnerability
CVE-2024-37965
Microsoft SQL Server Elevation of Privilege Vulnerability
CVE-2024-37980
Microsoft SQL Server Elevation of Privilege Vulnerability
CVE-2024-38014
Home windows Installer Elevation of Privilege Vulnerability
CVE-2024-38046
PowerShell Elevation of Privilege Vulnerability
CVE-2024-38188
Azure Community Watcher VM Agent Elevation of Privilege Vulnerability
CVE-2024-38225
Microsoft Dynamics 365 Enterprise Central Elevation of Privilege Vulnerability
CVE-2024-38237
Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability
CVE-2024-38238
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38239
Home windows Kerberos Elevation of Privilege Vulnerability
CVE-2024-38240
Home windows Distant Entry Connection Supervisor Elevation of Privilege Vulnerability
CVE-2024-38241
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38242
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38243
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38244
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38245
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38246
Win32k Elevation of Privilege Vulnerability
CVE-2024-38247
Home windows Graphics Element Elevation of Privilege Vulnerability
CVE-2024-38248
Home windows Storage Elevation of Privilege Vulnerability
CVE-2024-38249
Home windows Graphics Element Elevation of Privilege Vulnerability
CVE-2024-38250
Home windows Graphics Element Elevation of Privilege Vulnerability
CVE-2024-38252
Home windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability
CVE-2024-38253
Home windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability
CVE-2024-43457
Home windows Setup and Deployment Elevation of Privilege Vulnerability
CVE-2024-43465
Microsoft Excel Elevation of Privilege Vulnerability
CVE-2024-43470
Azure Community Watcher VM Agent Elevation of Privilege Vulnerability
CVE-2024-43492
Microsoft AutoUpdate (MAU) Elevation of Privilege Vulnerability
Distant Code Execution (23 CVEs)
Vital severity
CVE-2024-38018
Microsoft SharePoint Server Distant Code Execution Vulnerability
CVE-2024-38119
Home windows Community Tackle Translation (NAT) Distant Code Execution Vulnerability
CVE-2024-43464
Microsoft SharePoint Server Distant Code Execution Vulnerability
CVE-2024-43491
Microsoft Home windows Replace Distant Code Execution Vulnerability
Vital severity
CVE-2024-21416
Home windows TCP/IP Distant Code Execution Vulnerability
CVE-2024-26186
Microsoft SQL Server Native Scoring Distant Code Execution Vulnerability
CVE-2024-26191
Microsoft SQL Server Native Scoring Distant Code Execution Vulnerability
CVE-2024-37335
Microsoft SQL Server Native Scoring Distant Code Execution Vulnerability
CVE-2024-37338
Microsoft SQL Server Native Scoring Distant Code Execution Vulnerability
CVE-2024-37339
Microsoft SQL Server Native Scoring Distant Code Execution Vulnerability
CVE-2024-37340
Microsoft SQL Server Native Scoring Distant Code Execution Vulnerability
CVE-2024-38045
Home windows TCP/IP Distant Code Execution Vulnerability
CVE-2024-38227
Microsoft SharePoint Server Distant Code Execution Vulnerability
CVE-2024-38228
Microsoft SharePoint Server Distant Code Execution Vulnerability
CVE-2024-38259
Microsoft Administration Console Distant Code Execution Vulnerability
CVE-2024-38260
Home windows Distant Desktop Licensing Service Distant Code Execution Vulnerability
CVE-2024-38263
Home windows Distant Desktop Licensing Service Distant Code Execution Vulnerability
CVE-2024-43454
Home windows Distant Desktop Licensing Service Distant Code Execution Vulnerability
CVE-2024-43463
Microsoft Workplace Visio Distant Code Execution Vulnerability
CVE-2024-43467
Home windows Distant Desktop Licensing Service Distant Code Execution Vulnerability
CVE-2024-43469
Azure CycleCloud Distant Code Execution Vulnerability
CVE-2024-43479
Microsoft Energy Automate Desktop Distant Code Execution Vulnerability
CVE-2024-43495
Home windows libarchive Distant Code Execution Vulnerability
Info Disclosure (11 CVEs)
Vital severity
CVE-2024-37337
Microsoft SQL Server Native Scoring Info Disclosure Vulnerability
CVE-2024-37342
Microsoft SQL Server Native Scoring Info Disclosure Vulnerability
CVE-2024-37966
Microsoft SQL Server Native Scoring Info Disclosure Vulnerability
CVE-2024-38254
Home windows Authentication Info Disclosure Vulnerability
CVE-2024-38256
Home windows Kernel-Mode Driver Info Disclosure Vulnerability
CVE-2024-38257
Microsoft AllJoyn API Info Disclosure Vulnerability
CVE-2024-38258
Home windows Distant Desktop Licensing Service Info Disclosure Vulnerability
CVE-2024-43458
Home windows Networking Info Disclosure Vulnerability
CVE-2024-43474
Microsoft SQL Server Info Disclosure Vulnerability
CVE-2024-43475
Microsoft Home windows Admin Middle Info Disclosure Vulnerability
CVE-2024-43482
Microsoft Outlook for iOS Info Disclosure Vulnerability
Denial of Service (8 CVEs)
Vital severity
CVE-2024-38230
Home windows Requirements-Based mostly Storage Administration Service Denial of Service Vulnerability
CVE-2024-38231
Home windows Distant Desktop Licensing Service Denial of Service Vulnerability
CVE-2024-38232
Home windows Networking Denial of Service Vulnerability
CVE-2024-38233
Home windows Networking Denial of Service Vulnerability
CVE-2024-38234
Home windows Networking Denial of Service Vulnerability
CVE-2024-38235
Home windows Hyper-V Denial of Service Vulnerability
CVE-2024-38236
DHCP Server Service Denial of Service Vulnerability
CVE-2024-43466
Microsoft SharePoint Server Denial of Service Vulnerability
Safety Function Bypass (4 CVEs)
Vital severity
CVE-2024-30073
Home windows Safety Zone Mapping Safety Function Bypass Vulnerability
CVE-2024-38217
Home windows Mark of the Net Safety Function Bypass Vulnerability
CVE-2024-38226
Microsoft Writer Safety Options Bypass Vulnerability
Reasonable severity
CVE-2024-43487
Home windows Mark of the Net Safety Function Bypass Vulnerability
Spoofing (3 CVEs)
Vital severity
CVE-2024-43455
Home windows Distant Desktop Licensing Service Spoofing Vulnerability
CVE-2024-43461
Home windows MSHTML Platform Spoofing Vulnerability
CVE-2024-43476
Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability
Appendix B: Exploitability
This can be a checklist of the September CVEs judged by Microsoft to be both below exploitation within the wild or extra prone to be exploited within the wild throughout the first 30 days post-release. The checklist is organized by CVE. Within the case of CVE-2024-43491, the problem itself just isn’t identified to be below lively exploit, however sure of the problems fastened by the rejected servicing-stack updates are, so we’re selecting to incorporate it on this checklist. (Please see the “Notable September updates” part above for context.)
Exploitation detected
CVE-2024-38014
Home windows Installer Elevation of Privilege Vulnerability
CVE-2024-38217
Home windows Mark of the Net Safety Function Bypass Vulnerability
CVE-2024-38226
Microsoft Writer Safety Options Bypass Vulnerability
CVE-2024-43491
Microsoft Home windows Replace Distant Code Execution Vulnerability
Exploitation extra possible throughout the subsequent 30 days
CVE-2024-38018
Microsoft SharePoint Server Distant Code Execution Vulnerability
CVE-2024-38227
Microsoft SharePoint Server Distant Code Execution Vulnerability
CVE-2024-38228
Microsoft SharePoint Server Distant Code Execution Vulnerability
CVE-2024-38237
Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability
CVE-2024-38238
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38241
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38242
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38243
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38244
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38245
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38246
Win32k Elevation of Privilege Vulnerability
CVE-2024-38247
Home windows Graphics Element Elevation of Privilege Vulnerability
CVE-2024-38249
Home windows Graphics Element Elevation of Privilege Vulnerability
CVE-2024-38252
Home windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability
CVE-2024-38253
Home windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability
CVE-2024-43457
Home windows Setup and Deployment Elevation of Privilege Vulnerability
CVE-2024-43461
Home windows MSHTML Platform Spoofing Vulnerability
CVE-2024-43464
Microsoft SharePoint Server Distant Code Execution Vulnerability
CVE-2024-43487
Home windows Mark of the Net Safety Function Bypass Vulnerability
Appendix C: Merchandise Affected
This can be a checklist of September’s patches sorted by product household, then sub-sorted by severity. Every checklist is additional organized by CVE. Patches which are shared amongst a number of product households are listed a number of instances, as soon as for every product household.
Home windows (47 CVEs)
Vital severity
CVE-2024-38119
Home windows Community Tackle Translation (NAT) Distant Code Execution Vulnerability
CVE-2024-43491
Microsoft Home windows Replace Distant Code Execution Vulnerability
Vital severity
CVE-2024-21416
Home windows TCP/IP Distant Code Execution Vulnerability
CVE-2024-30073
Home windows Safety Zone Mapping Safety Function Bypass Vulnerability
CVE-2024-38014
Home windows Installer Elevation of Privilege Vulnerability
CVE-2024-38045
Home windows TCP/IP Distant Code Execution Vulnerability
CVE-2024-38046
PowerShell Elevation of Privilege Vulnerability
CVE-2024-38217
Home windows Mark of the Net Safety Function Bypass Vulnerability
CVE-2024-38230
Home windows Requirements-Based mostly Storage Administration Service Denial of Service Vulnerability
CVE-2024-38231
Home windows Distant Desktop Licensing Service Denial of Service Vulnerability
CVE-2024-38232
Home windows Networking Denial of Service Vulnerability
CVE-2024-38233
Home windows Networking Denial of Service Vulnerability
CVE-2024-38234
Home windows Networking Denial of Service Vulnerability
CVE-2024-38235
Home windows Hyper-V Denial of Service Vulnerability
CVE-2024-38236
DHCP Server Service Denial of Service Vulnerability
CVE-2024-38237
Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability
CVE-2024-38238
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38239
Home windows Kerberos Elevation of Privilege Vulnerability
CVE-2024-38240
Home windows Distant Entry Connection Supervisor Elevation of Privilege Vulnerability
CVE-2024-38241
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38242
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38243
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38244
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38245
Kernel Streaming Service Driver Elevation of Privilege Vulnerability
CVE-2024-38246
Win32k Elevation of Privilege Vulnerability
CVE-2024-38247
Home windows Graphics Element Elevation of Privilege Vulnerability
CVE-2024-38248
Home windows Storage Elevation of Privilege Vulnerability
CVE-2024-38249
Home windows Graphics Element Elevation of Privilege Vulnerability
CVE-2024-38252
Home windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability
CVE-2024-38253
Home windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability
CVE-2024-38254
Home windows Authentication Info Disclosure Vulnerability
CVE-2024-38256
Home windows Kernel-Mode Driver Info Disclosure Vulnerability
CVE-2024-38257
Microsoft AllJoyn API Info Disclosure Vulnerability
CVE-2024-38258
Home windows Distant Desktop Licensing Service Info Disclosure Vulnerability
CVE-2024-38259
Microsoft Administration Console Distant Code Execution Vulnerability
CVE-2024-38260
Home windows Distant Desktop Licensing Service Distant Code Execution Vulnerability
CVE-2024-38263
Home windows Distant Desktop Licensing Service Distant Code Execution Vulnerability
CVE-2024-43454
Home windows Distant Desktop Licensing Service Distant Code Execution Vulnerability
CVE-2024-43455
Home windows Distant Desktop Licensing Service Spoofing Vulnerability
CVE-2024-43457
Home windows Setup and Deployment Elevation of Privilege Vulnerability
CVE-2024-43458
Home windows Networking Info Disclosure Vulnerability
CVE-2024-43461
Home windows MSHTML Platform Spoofing Vulnerability
CVE-2024-43467
Home windows Distant Desktop Licensing Service Distant Code Execution Vulnerability
CVE-2024-43475
Microsoft Home windows Admin Middle Info Disclosure Vulnerability
CVE-2024-43495
Home windows libarchive Distant Code Execution Vulnerability
Reasonable severity
CVE-2024-43487
Home windows Mark of the Net Safety Function Bypass Vulnerability
SQL Server (13 CVEs)
Vital severity
CVE-2024-26186
Microsoft SQL Server Native Scoring Distant Code Execution Vulnerability
CVE-2024-26191
Microsoft SQL Server Native Scoring Distant Code Execution Vulnerability
CVE-2024-37335
Microsoft SQL Server Native Scoring Distant Code Execution Vulnerability
CVE-2024-37337
Microsoft SQL Server Native Scoring Info Disclosure Vulnerability
CVE-2024-37338
Microsoft SQL Server Native Scoring Distant Code Execution Vulnerability
CVE-2024-37339
Microsoft SQL Server Native Scoring Distant Code Execution Vulnerability
CVE-2024-37340
Microsoft SQL Server Native Scoring Distant Code Execution Vulnerability
CVE-2024-37341
Microsoft SQL Server Elevation of Privilege Vulnerability
CVE-2024-37342
Microsoft SQL Server Native Scoring Info Disclosure Vulnerability
CVE-2024-37965
Microsoft SQL Server Elevation of Privilege Vulnerability
CVE-2024-37966
Microsoft SQL Server Native Scoring Info Disclosure Vulnerability
CVE-2024-37980
Microsoft SQL Server Elevation of Privilege Vulnerability
CVE-2024-43474
Microsoft SQL Server Info Disclosure Vulnerability
Azure (6 CVEs)
Vital severity
CVE-2024-38194
Azure Net Apps Elevation of Privilege Vulnerability
CVE-2024-38216
Azure Stack Hub Elevation of Privilege Vulnerability
CVE-2024-38220
Azure Stack Hub Elevation of Privilege Vulnerability
Vital severity
CVE-2024-38188
Azure Community Watcher VM Agent Elevation of Privilege Vulnerability
CVE-2024-43469
Azure CycleCloud Distant Code Execution Vulnerability
CVE-2024-43470
Azure Community Watcher VM Agent Elevation of Privilege Vulnerability
SharePoint (5 CVEs)
Vital severity
CVE-2024-38018
Microsoft SharePoint Server Distant Code Execution Vulnerability
CVE-2024-43464
Microsoft SharePoint Server Distant Code Execution Vulnerability
Vital severity
CVE-2024-38227
Microsoft SharePoint Server Distant Code Execution Vulnerability
CVE-2024-38228
Microsoft SharePoint Server Distant Code Execution Vulnerability
CVE-2024-43466
Microsoft SharePoint Server Denial of Service Vulnerability
Workplace (4 CVE)
Vital severity
CVE-2024-38226
Microsoft Writer Safety Options Bypass Vulnerability
CVE-2024-38250
Home windows Graphics Element Elevation of Privilege Vulnerability
CVE-2024-43463
Microsoft Workplace Visio Distant Code Execution Vulnerability
CVE-2024-43465
Microsoft Excel Elevation of Privilege Vulnerability
365 (2 CVE)
Vital severity
CVE-2024-43463
Microsoft Workplace Visio Distant Code Execution Vulnerability
CVE-2024-43465
Microsoft Excel Elevation of Privilege Vulnerability
Dynamics 365 (2 CVE)
Vital severity
CVE-2024-38225
Microsoft Dynamics 365 Enterprise Central Elevation of Privilege Vulnerability
CVE-2024-43476
Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability
Microsoft AutoUpdate (MAU) for Mac (1 CVE)
Vital severity
CVE-2024-43492
Microsoft AutoUpdate (MAU) Elevation of Privilege Vulnerability
Outlook for iOS (1 CVE)
Vital severity
CVE-2024-43482
Microsoft Outlook for iOS Info Disclosure Vulnerability
PowerBI (1 CVE)
Vital severity
CVE-2024-43479
Microsoft Energy Automate Desktop Distant Code Execution Vulnerability
Visio (1 CVE)
Vital severity
CVE-2024-43463
Microsoft Workplace Visio Distant Code Execution Vulnerability
Appendix D: Advisories and Different Merchandise
This can be a checklist of advisories and knowledge on different related CVEs within the September launch, sorted by product.
Related to Adobe (non-Microsoft launch) (3 CVEs)
CVE-2024-41869
APSB24-70
Use After Free (CWE-416)
CVE-2024-41874
APSB24-71
Deserialization of Untrusted Information (CWE-502)
CVE-2024-39420
APSB24-70
Time-of-check Time-of-use (TOCTOU) Race Situation (CWE-367)