To deploy a ransomware assault, adversaries should first acquire entry to a sufferer’s company surroundings, units, and information. Risk actors sometimes use two predominant approaches to achieve entry: logging in utilizing compromised credentials, i.e., reputable entry information that had beforehand been stolen, and exploiting vulnerabilities in functions and instruments utilized by the enterprise. Different much less frequent modes of entry embrace brute drive assaults, provide chain compromise, malicious emails/paperwork, and adware. Phishing options closely in ransomware assaults however is primarily used to steal the credentials later used to log in to the group.
This report highlights how ransomware outcomes differ relying on the basis reason behind the assault. It compares the severity, monetary value, and operational impression of assaults that begin with an exploited vulnerability with these the place adversaries use compromised credentials to penetrate the group. It additionally identifies the {industry} sectors most and least generally exploited.
The findings are primarily based on a vendor-agnostic survey commissioned by Sophos of two,974 IT/cybersecurity professionals in small and mid-sized organizations (100-5,000 workers) that had been hit by ransomware within the final 12 months. The survey was performed by impartial analysis company Vanson Bourne in early 2024 and displays respondents’ experiences over the earlier 12 months.
>> Obtain the PDF copy of the report
Government abstract
Whereas all ransomware assaults have destructive outcomes, those who begin by exploiting unpatched vulnerabilities are notably brutal for his or her victims. Organizations hit by assaults that started on this method report significantly extra extreme outcomes than these whose assaults began with compromised credentials, together with the next propensity to:
Have backups compromised (75% success price vs. 54% for compromised credentials)
Have information encrypted (67% encryption price vs. 43% for compromised credentials)
Pay the ransom (71% cost price vs. 45% for compromised credentials)
Cowl the complete value of the ransom in-house (31% funded the complete ransom in-house vs. 2% for compromised credentials)
Additionally they reported:
4X greater general assault restoration prices ($3M vs. $750k for compromised credentials)
Slower restoration time (45% took greater than a month vs. 37% for compromised credentials)
The research focuses on correlation, and additional exploration is required into causes behind these outcomes. It’s necessary to keep in mind that not all ransomware assaults are equal. Some are executed by subtle, well-funded gangs utilizing a spread of revolutionary approaches. On the identical time, using crude, low cost ransomware by lower-skilled menace actors is on the rise. It could be that adversaries which can be in a position to exploit unpatched software program vulnerabilities are extra expert than attackers who purchase stolen credentials from the darkish net (for instance), and subsequently higher in a position to reach compromising backups and encrypting information.
One-third of ransomware assaults begin with an unpatched vulnerability
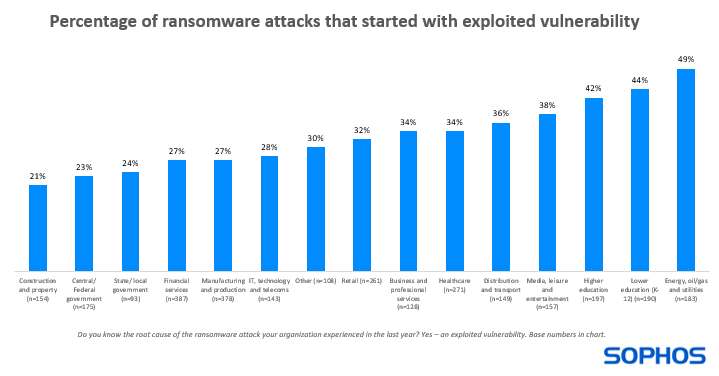
32% of ransomware assaults skilled by the survey respondents prior to now 12 months began with an exploited vulnerability. Diving deeper, we see that the proportion of ransomware assaults that started on this method varies significantly by {industry}:
Highest: power, oil/fuel, and utilities – 49% of assaults
Lowest: building and property – 21% of assaults
This variation is probably going impacted, partly, by the completely different know-how options used and their related patching challenges. Sectors equivalent to power, oil/fuel, and utilities sometimes use the next proportion of older applied sciences extra susceptible to safety gaps than many different sectors, and patches is probably not obtainable for legacy and end-of-life options.
On the identical time, most of the time, patches can be found – they only haven’t been utilized. Of the assaults that Sophos incident responders have been introduced in to remediate in 2022 that began with exploited vulnerabilities, over half (55%) have been attributable to ProxyShell and Log4Shell — each of which had current patches on the time of compromise. Sophos continues to see ProxyShell being exploited 30 months after the discharge of the patch. Be taught extra.
The evaluation additionally revealed that the propensity to expertise an exploit-led assault varies by group dimension:
26% of ransomware assaults in small companies (sub $50M annual income)
30% of ransomware assaults in mid-sized companies ($50M-$1B)
37% of ransomware assaults in giant companies ($1B+)
As organizations develop, their IT infrastructures are likely to develop with them. The bigger the surroundings, the better the problem in understanding the assault floor and the extra instruments and applied sciences that should be maintained.
Ransomware impacts are extra extreme when the assault begins with an exploited vulnerability
The ultimate objective for a ransomware actor is to encrypt a corporation’s information and extract a ransom cost in return for the decryption key. On the best way, they nearly at all times try to compromise their sufferer’s backups to cut back their means to revive information with out paying.
The evaluation reveals that throughout all three factors – backup compromise, information encryption, and ransom cost – the impacts are most extreme when the assault begins with an exploited vulnerability.
Backup compromise
There is no such thing as a distinction in attackers’ propensity to try to compromise backups primarily based on the basis trigger. Adversaries tried to compromise them in 96% of assaults that began with exploited vulnerabilities and compromised credentials. Nonetheless, there’s a appreciable distinction of their success price:
75% of makes an attempt have been profitable when the assault began with an exploited vulnerability
54% of makes an attempt have been profitable when the assault began with compromised credentials
This can be as a result of adversaries who leverage unpatched vulnerabilities are extra expert at breaching backups. It could additionally mirror that organizations with an uncovered assault floor have weaker backup safety. Regardless of the trigger, having your backups compromised reduces resilience in opposition to the complete impression of the assault.
Knowledge encryption
Organizations are greater than 50% extra prone to have their information encrypted when an assault begins with an exploited vulnerability reasonably than compromised credentials:
67% of assaults resulted in information encryption when the assault began with an exploited vulnerability
43% of assaults resulted in information encryption when the assault began with compromised credentials
As with backup compromise, the distinction in final result by root trigger might mirror differing ability ranges in adversary teams and variations within the general power of a corporation’s cyber defenses.
Ransom cost price
Given the upper price of backup compromise reported when the assault began with an exploited vulnerability, it’s maybe no shock that this group reported the next propensity to pay the ransom:
71% of organizations that had information encrypted paid the ransom when the assault began with an exploited vulnerability
45% of organizations that had information encrypted paid the ransom when the assault began with compromised credentials
With out backups to recuperate from, the stress on ransomware victims to entry the decryption key will increase, possible driving organizations to work with the attackers to revive information.
Unpatched vulnerabilities have business-critical penalties
Ransomware assaults that begin with an exploited vulnerability have significantly better monetary and operational impression than those who start with compromised credentials.
Ransom cost
Whereas the assault root trigger has an nearly negligible impression on the ransom cost sum, with the median quantity coming in at $1.988M (exploited vulnerabilities) and $2M (compromised credentials), it does have a substantial impression on the funding of the ransom cost:
31% of organizations funded the complete ransom in-house when the assault began with an exploited vulnerability
2% of organizations funded the complete ransom in-house when the assault began with compromised credentials
Mother or father corporations and cyber insurance coverage suppliers usually tend to contribute to the ransom when the assault begins with compromised credentials reasonably than an exploited vulnerability.
Trying extra broadly on the propensity of insurance coverage carriers to honor claims we see that one quarter (25%) of denied claims by organizations that skilled an exploited vulnerability have been resulting from not having the required cyber defenses for the declare to be honored, in comparison with 12% of claims the place adversaries used compromised credentials.
Restoration value
The ransom is only one factor that contributes to the general restoration value from a ransomware assault. Leaving apart any ransom paid, the median general restoration value for ransomware assaults that begin with an exploited vulnerability ($3M) is 4 instances better than for those who start with compromised credentials ($750K).
Restoration time
Recovering from an assault that begins with an exploited vulnerability is often a lot slower than when the basis trigger is compromised credentials.
45% took greater than a month to recuperate when the assault began with an exploited vulnerability
37% took greater than a month to recuperate when the assault began with compromised credentials
This discovering possible displays the completely different remediation actions that victims have to undertake relying on the basis trigger, and their respective operational overheads. Patching a system or upgrading from an end-of-life product to a supported model might be extra time-consuming than resetting credentials. It could even be a results of the better injury attributable to exploited vulnerability assaults, together with a better probability of backup compromise and information encryption.
Suggestions
Patching is a crucial first step in decreasing the danger of falling sufferer to a ransomware assault (or every other breach) that begins with an exploited vulnerability. Should you repair the safety hole, adversaries can’t exploit it. It ought to ideally be a part of a broader exploit-prevention danger administration technique:
Decrease your assault floor
Keep full visibility of all of your external-facing belongings to know what you’re coping with and keep away from blind spots.
Patch utilizing risk-based prioritization. With new exploits found sooner than most organizations can repair them, focus your efforts the place they are going to have essentially the most impression. This implies figuring out and prioritizing the patching of high-risk exposures.
Replace usually. Utilizing the newest model of an utility or software ensures you profit from the distributors’ most up-to-date safety fixes.
Deploy anti-exploit protections
Whereas the variety of exploitable vulnerabilities continues to develop quickly, attackers can solely leverage a restricted variety of methods to use. Constructed-in anti-exploitation capabilities in endpoint safety options cease the behaviors utilized in these assaults – together with with zero-day vulnerabilities for which no patch has but been launched.
Detect and reply to suspicious actions
Know-how alone can’t cease each assault. Adversaries are expert at leveraging reputable IT instruments and stolen credentials, adapting their method on the fly to keep away from detection. Stopping superior, human-led ransomware assaults and breaches requires 24/7 detection and response throughout your surroundings, delivered by a specialist supplier or highly-skilled in-house group.
How Sophos can assist
Sophos Managed Danger
Sophos Managed Danger is a vulnerability and assault floor administration service powered by industry-leading Tenable know-how and delivered by a devoted group of Sophos menace publicity and remediation specialists. It addresses 4 vital use circumstances: assault floor visibility, steady danger monitoring, vulnerability prioritization, and quick identification of latest dangers.
Sophos Managed Danger is obtainable with Sophos MDR, a totally managed cybersecurity service delivered 24/7 by Sophos menace specialists. A devoted group of Sophos Managed Danger operators – extremely expert in vulnerabilities and menace exposures – works intently with Sophos MDR analysts across the clock.
Sophos Endpoint
Sophos Endpoint contains greater than 60 anti-exploitation capabilities that block the behaviors adversaries use to use an unpatched vulnerability, stopping each identified vulnerabilities and zero-day threats. The anti-exploit capabilities deploy routinely from day one with no configuration or want for wonderful tuning.
Sophos Endpoint takes a complete method to safety with out counting on one safety approach. Net, utility, and peripheral controls scale back your menace floor and block frequent assault vectors. AI, behavioral evaluation, anti-ransomware, and different state-of-the-art applied sciences cease threats quick earlier than they escalate.
>> Obtain the PDF copy of the report