Amazon Bedrock is a completely managed service supplied by AWS that gives builders entry to basis fashions (FMs) and the instruments to customise them for particular purposes. It permits builders to construct and scale generative AI purposes utilizing FMs via an API, with out managing infrastructure. You’ll be able to select from numerous FMs from Amazon and main AI startups corresponding to AI21 Labs, Anthropic, Cohere, and Stability AI to seek out the mannequin that’s finest suited on your use case. With the Amazon Bedrock serverless expertise, you’ll be able to rapidly get began, simply experiment with FMs, privately customise them with your individual information, and seamlessly combine and deploy them into your purposes utilizing AWS instruments and capabilities.
Clients are constructing revolutionary generative AI purposes utilizing Amazon Bedrock APIs utilizing their very own proprietary information. When accessing Amazon Bedrock APIs, clients are searching for mechanism to arrange an information perimeter with out exposing their information to web to allow them to mitigate potential menace vectors from web publicity. The Amazon Bedrock VPC endpoint powered by AWS PrivateLink lets you set up a personal connection between the VPC in your account and the Amazon Bedrock service account. It permits VPC situations to speak with service sources with out the necessity for public IP addresses.
On this publish, we exhibit the best way to arrange non-public entry in your AWS account to entry Amazon Bedrock APIs over VPC endpoints powered by PrivateLink that will help you construct generative AI purposes securely with your individual information.
Answer overview
You should utilize generative AI to develop a various vary of purposes, corresponding to textual content summarization, content material moderation, and different capabilities. When constructing such generative AI purposes utilizing FMs or base fashions, clients wish to generate a response with out going over the general public web or based mostly on their proprietary information which will reside of their enterprise databases.
Within the following diagram, we depict an structure to arrange your infrastructure to learn your proprietary information residing in Amazon Relational Database Service (Amazon RDS) and increase the Amazon Bedrock API request with product data when answering product-related queries out of your generative AI software. Though we use Amazon RDS on this diagram for illustration functions, you’ll be able to check the non-public entry of the Amazon Bedrock APIs finish to finish utilizing the directions supplied on this publish.
The workflow steps are as follows:
AWS Lambda working in your non-public VPC subnet receives the immediate request from the generative AI software.
Lambda makes a name to proprietary RDS database and augments the immediate question context (for instance, including product data) and invokes the Amazon Bedrock API with the augmented question request.
The API name is routed to the Amazon Bedrock VPC endpoint that’s related to the VPC endpoint coverage with Permit permissions to Amazon Bedrock APIs.
The Amazon Bedrock service API endpoint receives the API request over PrivateLink with out traversing the general public web.
You’ll be able to change the Amazon Bedrock VPC endpoint coverage to Deny permissions to validate that Amazon Bedrock APIs calls are denied.
You may also privately entry Amazon Bedrock APIs over the VPC endpoint out of your company community via an AWS Direct Join gateway.
Conditions
Earlier than you get began, ensure you have the next conditions:
An AWS account
An AWS Id and Entry Administration (IAM) federation position with entry to do the next:
Create, edit, view, and delete VPC community sources
Create, edit, view and delete Lambda capabilities
Create, edit, view and delete IAM roles and insurance policies
Listing basis fashions and invoke the Amazon Bedrock basis mannequin
For this publish, we use the us-east-1 Area
Request basis mannequin entry through the Amazon Bedrock console
Arrange the non-public entry infrastructure
On this part, we arrange the infrastructure corresponding to VPC, non-public subnets, safety teams, and Lambda operate utilizing an AWS CloudFormation template.
Use the next template to create the infrastructure stack Bedrock-GenAI-Stack in your AWS account.
The CloudFormation template creates the next sources in your behalf:
A VPC with two non-public subnets in separate Availability Zones
Safety teams and routing tables
IAM position and insurance policies to be used by Lambda, Amazon Bedrock, and Amazon Elastic Compute Cloud (Amazon EC2)
Arrange the VPC endpoint for Amazon Bedrock
On this part, we use Amazon Digital Personal Cloud (Amazon VPC) to arrange the VPC endpoint for Amazon Bedrock to facilitate non-public connectivity out of your VPC to Amazon Bedrock.
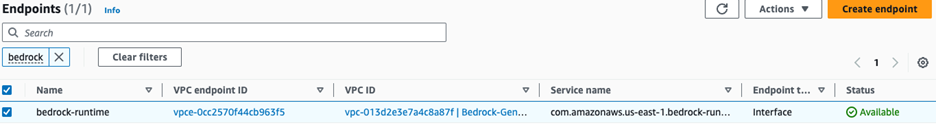
On the Amazon VPC console, beneath Digital non-public cloud within the navigation pane, select Endpoints.
Select Create endpoint.
For Identify tag, enter bedrock-vpce.
Beneath Companies, seek for bedrock-runtime and choose com.amazonaws.<area>.bedrock-runtime.
For VPC, specify the VPC Bedrock-GenAI-Undertaking-vpc that you simply created via the CloudFormation stack within the earlier part.
Within the Subnets part, and choose the Availability Zones and select the corresponding subnet IDs from the drop-down menu.
For Safety teams, choose the safety group with the group identify Bedrock-GenAI-Stack-VPCEndpointSecurityGroup- and outline Permit TLS for VPC Endpoint.
A safety group acts as a digital firewall on your occasion to regulate inbound and outbound visitors. Be aware that this VPC endpoint safety group solely permits visitors originating from the safety group hooked up to your VPC non-public subnets, including a layer of safety.

Select Create endpoint.
Within the Coverage part, choose Customized and enter the next least privilege coverage to make sure solely sure actions are allowed on the desired basis mannequin useful resource, arn:aws:bedrock:*::foundation-model/anthropic.claude-instant-v1 for a given principal (corresponding to Lambda operate IAM position).
It might take as much as 2 minutes till the interface endpoint is created and the standing modifications to Out there. You’ll be able to refresh the web page to test the most recent standing.
Arrange the Lambda operate over non-public VPC subnets
Full the next steps to configure the Lambda operate:
On the Lambda console, select Features within the navigation pane.
Select the operate gen-ai-lambda-stack-BedrockTestLambdaFunction-XXXXXXXXXXXX.
On the Configuration tab, select Permissions within the left pane.
Beneath Execution position¸ select the hyperlink for the position gen-ai-lambda-stack-BedrockTestLambdaFunctionRole-XXXXXXXXXXXX.
You’re redirected to the IAM console.
Within the Permissions insurance policies part, select Add permissions and select Create inline coverage.
On the JSON tab, modify the coverage as follows:
Select Subsequent.
For Coverage identify, enter enivpce-policy.
Select Create coverage.
Add the next inline coverage (present your supply VPC endpoints) for proscribing Lambda entry to Amazon Bedrock APIs solely through VPC endpoints:
On Lambda operate web page, on the Configuration tab, select VPC within the left pane, then select Edit.
For VPC, select Bedrock-GenAI-Undertaking-vpc.
For Subnets, select the non-public subnets.
For Safety teams, select gen-ai-lambda-stack-SecurityGroup- (the safety group for the Amazon Bedrock workload in non-public subnets).
Select Save.
Take a look at non-public entry controls
Now you’ll be able to check the non-public entry controls (Amazon Bedrock APIs over VPC endpoints).
On the Lambda console, select Features within the navigation pane.
Select the operate gen-ai-lambda-stack-BedrockTestLambdaFunction-XXXXXXXXXXXX.
On the Code tab, select Take a look at.
It is best to see the next response from the Amazon Bedrock API name (Standing: Succeeded).

To disclaim entry to Amazon Bedrock APIs over VPC endpoints, navigate to the Amazon VPC console.
Beneath Digital non-public cloud within the navigation pane, select Endpoints.
Select your coverage and navigate to the Coverage tab.
Presently, the VPC endpoint coverage is ready to Permit.
To disclaim entry, select Edit Coverage.
Change Permit to Deny and select Save.
It might take as much as 2 minutes for the coverage for the VPC endpoint to replace.
Return to the Lambda operate web page and on the Code tab, select Take a look at.
As proven within the following screenshot, the entry request to Amazon Bedrock over the VPC endpoint was denied (Standing: Failed).

Via this testing course of, we demonstrated how visitors out of your VPC to the Amazon Bedrock API endpoint is traversing over the PrivateLink connection and never via the web connection.
Clear up
Comply with these steps to keep away from incurring future prices:
Clear up the VPC endpoints.
Clear up the VPC.
Delete the CloudFormation stack.
Conclusion
On this publish, we demonstrated the best way to arrange and operationalize a personal connection between a generative AI workload deployed in your buyer VPC and Amazon Bedrock utilizing an interface VPC endpoint powered by PrivateLink. When utilizing the structure mentioned on this publish, the visitors between your buyer VPC and Amazon Bedrock is not going to depart the Amazon community, guaranteeing your information is just not uncovered to the general public web and thereby serving to together with your compliance necessities.
As a subsequent step, attempt the answer out in your account and share your suggestions.
Concerning the Authors
 Ram Vittal is a Principal ML Options Architect at AWS. He has over 3 a long time of expertise architecting and constructing distributed, hybrid, and cloud purposes. He’s enthusiastic about constructing safe and scalable AI/ML and large information options to assist enterprise clients with their cloud adoption and optimization journey to enhance their enterprise outcomes. In his spare time, he rides his motorbike and walks together with his 3-year-old Sheepadoodle!
Ram Vittal is a Principal ML Options Architect at AWS. He has over 3 a long time of expertise architecting and constructing distributed, hybrid, and cloud purposes. He’s enthusiastic about constructing safe and scalable AI/ML and large information options to assist enterprise clients with their cloud adoption and optimization journey to enhance their enterprise outcomes. In his spare time, he rides his motorbike and walks together with his 3-year-old Sheepadoodle!
 Ray Khorsandi is an AI/ML specialist at AWS, supporting strategic clients with AI/ML finest practices. With an M.Sc. and Ph.D. in Electrical Engineering and Laptop Science, he leads enterprises to construct safe, scalable AI/ML and large information options to optimize their cloud adoption. His passions embrace laptop imaginative and prescient, NLP, generative AI, and MLOps. Ray enjoys enjoying soccer and spending high quality time with household.
Ray Khorsandi is an AI/ML specialist at AWS, supporting strategic clients with AI/ML finest practices. With an M.Sc. and Ph.D. in Electrical Engineering and Laptop Science, he leads enterprises to construct safe, scalable AI/ML and large information options to optimize their cloud adoption. His passions embrace laptop imaginative and prescient, NLP, generative AI, and MLOps. Ray enjoys enjoying soccer and spending high quality time with household.
 Michael Daniels is an AI/ML Specialist at AWS. His experience lies in constructing and main AI/ML and generative AI options for advanced and difficult enterprise issues, which is enhanced by his Ph.D. from the Univ. of Texas and his M.Sc. in Laptop Science specialization in Machine Studying from the Georgia Institute of Expertise. He excels in making use of cutting-edge cloud applied sciences to innovate, encourage, and remodel industry-leading organizations, whereas additionally successfully speaking with stakeholders at any stage or scale. In his spare time, you’ll be able to catch Michael snowboarding or snowboarding within the mountains.
Michael Daniels is an AI/ML Specialist at AWS. His experience lies in constructing and main AI/ML and generative AI options for advanced and difficult enterprise issues, which is enhanced by his Ph.D. from the Univ. of Texas and his M.Sc. in Laptop Science specialization in Machine Studying from the Georgia Institute of Expertise. He excels in making use of cutting-edge cloud applied sciences to innovate, encourage, and remodel industry-leading organizations, whereas additionally successfully speaking with stakeholders at any stage or scale. In his spare time, you’ll be able to catch Michael snowboarding or snowboarding within the mountains.









/cdn.vox-cdn.com/uploads/chorus_asset/file/24090208/STK171_VRG_Illo_9_Normand_ElonMusk_09.jpg)















