In our earlier article we’ve got demonstrated a working prototype of Host Identification Based mostly Digital Personal Service or HIP-VPLS. Again then we used the Mininet framework. Right here we’re going to exhibit easy methods to deploy this method on an actual {hardware}. We’re going to use NanoPi R2S because the platform for HIP-VPLS. Only a reminder. Digital Personal LAN Providers (VPLS) present means for constructing Layer 2 communication on prime of an current IP community. VPLS could be constructed utilizing varied approaches. Nonetheless, when constructing a production-grade VPLS answer one must have a transparent image of how such facets as safety, mobility, and L2 points shall be solved.
Host Identification Protocol (HIP) was initially designed to separate the twin position of the IP addresses. In different phrases, HIP is a Layer 3.5 answer that sits between the IP and transport layers. HIP makes use of hashes of public keys as identifiers. These identifiers, or Host Identification Tags (HITs), are uncovered to the transport layer and by no means change (properly, strictly talking, they could change if the system administrator will determine to rotate the RSA or ECDSA key pairs as an illustration, however that may occur hardly ever). However, HIP makes use of routable IP addresses (these could be each IPv4 or IPv6) as locators and are used to ship the HIP and IPSec packets between the end-points. General, to determine one another and change secret keys, HIP depends on a 4-way handshake (often known as HIP base change, or HIP BEX for brief). Throughout the BEX, friends negotiate a set of cryptographic algorithms for use, determine one another (since HITs are everlasting and are sure to public keys HIP can make use of a easy firewall primarily based on HITs to filter out untrusted connections), change the keys (HIP can use Diffie-Hellman and Elliptic Curve Diffie-Hellman algorithms), and even shield from Denial of Service assaults utilizing computational puzzles (these are primarily based on cryptographic hash capabilities and skill of friends to search out collisions in hash capabilities; the complexity of an answer is regulated by a responder in HIP BEX). HIP additionally helps mobility and makes use of a separate handshake process throughout which the peer notifies its counterpart in regards to the modifications within the locator (learn the IP handle used for routing functions).
{Hardware}
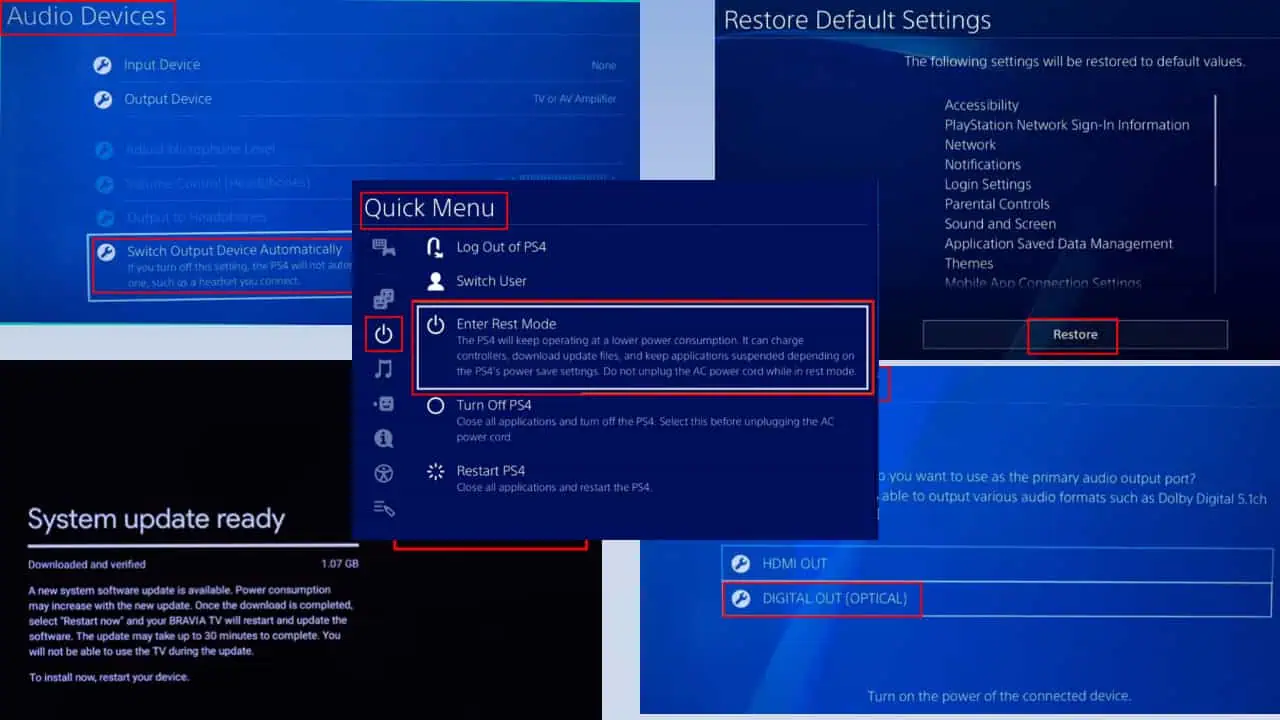
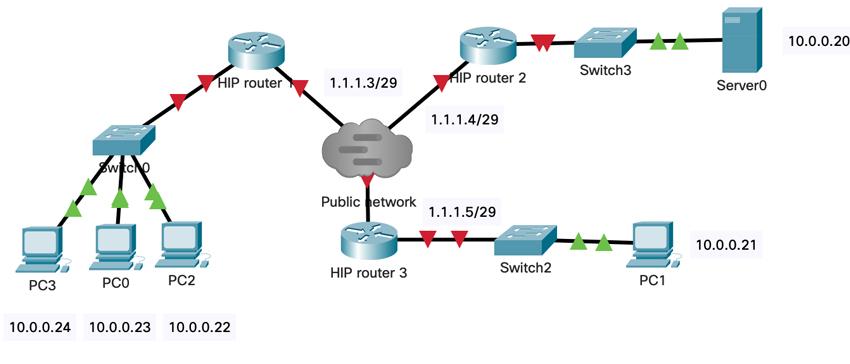
In our deployment we’ve got used the next setup. For HIP switches we’ve got used the NanoPI R2S computing platform. We’ve used 8 port SNR switches to attach 3 NanoPI R2S that method we’ve got mimicked the IP overlay within the setup. NanoPI R2S has two interfaces: one is dealing with LAN community, the opposite one is dealing with the WAN community. NanoPI R2S has the next traits: it has 1GB of reminiscence, quad core CPU, 32GB SD card. To wire the routers we’ve got used SNR switches (every change had 8 1 GB/s ports, and two Small Type Issue (SFP) slots. The testbed configuration is proven on the determine beneath:
Deploying the system
To deploy the system, we’ve got ready an FriendlyWRT Linux picture and flushed it on SD playing cards.
We then inserted the playing cards into NanoPI R2S and ran the next instructions:
$ git clone https://github.com/strangebit-io/hip-vpls-hw
Subsequent, we’ve got run the next instructions on every router:
#!/bin/bash
cd hip-vpls-hw
echo “Updating the system”
opkg replace
echo “Putting in libraries”
opkg set up nano
opkg set up rsync
opkg set up python3
opkg set up python3-pip
opkg set up python3-netifaces
pip3 set up pycryptodome
opkg set up python3-netifaces
echo “Getting ready directories”
mkdir /choose/hip-vpls/
cd ..
echo “Copying the recordsdata”
rsync -rv hiplib switchd.py switchfabric.py /choose/hip-vpls/
echo “Copying the service file”
cd startup
cp hip-vpls /and many others/init.d/
chmod +x /and many others/init.d/hip-vpls
/and many others/init.d/hip-vpls allow
/and many others/init.d/hip-vpls begin
One attention-grabbing configuration possibility that we would have liked to set was associated to promiscuous mode of the Ethernet card (in any other case the uncooked socket was not choosing the unicast frames). So, we’ve got modified the interface configuration as follows:
config interface ‘loopback’
possibility gadget ‘lo’
possibility proto ‘static’
possibility ipaddr ‘127.0.0.1’
possibility netmask ‘255.0.0.0’
config globals ‘globals’
possibility ula_prefix ‘fd00:ab:cd::/48’
config gadget
possibility title ‘eth0’
possibility macaddr ‘3e:25:61:94:f3:36’
config interface ‘wan’
possibility gadget ‘eth0’
possibility proto ‘static’
possibility ipaddr ‘1.1.1.4’
possibility netmask ‘255.255.255.248’
config gadget
possibility title ‘eth1’
possibility macaddr ‘3e:25:61:94:f3:37’
possibility promisc ‘1’
config interface ‘lan’
possibility gadget ‘eth1’
We’ve additionally reconfigured the firewall guidelines to permit all community visitors to move by way of the router.
We then generated HITs for every HIP change, configured hosts file and firewall guidelines (the configuration was beforehand described right here
Experimental analysis
General, the deployed system appeared like this:
Utilizing the IPERF instrument we’ve got measured the throughput between PC3 and Server0. The outcomes weren’t so fascinating: we’ve got obtained 1.5Mb/s throughput on a 1GB/s hyperlinks. We’re going to proceed to enhance the efficiency of the HIP-VPLS – at present we try to compile the supply code into C code.